With configurable user selection dialogs, it provides a user-friendly experience while maintaining strict security. As you discover the hidden depths of the web, ensure your sensitive data remains protected, no matter where it travels. Several dark web search engines allow people to explore this hidden part of the internet.
Browse The Dark Web Safely
The technology behind the darknet is actively maintained and continues to evolve. This increases the accessibility and sophistication of cyber threats, with far-reaching consequences for businesses. To secure against these risks, organizations invest in robust cybersecurity strategies, conduct regular security assessments, and educate employees to recognize and mitigate threats. The Hidden Wiki contains links to a variety of content, including forums, marketplaces, and other hidden services, many of which offer products or services that may be illegal or illicit.
Dark Web Search: The Best Dark Web Search Engines In 2025
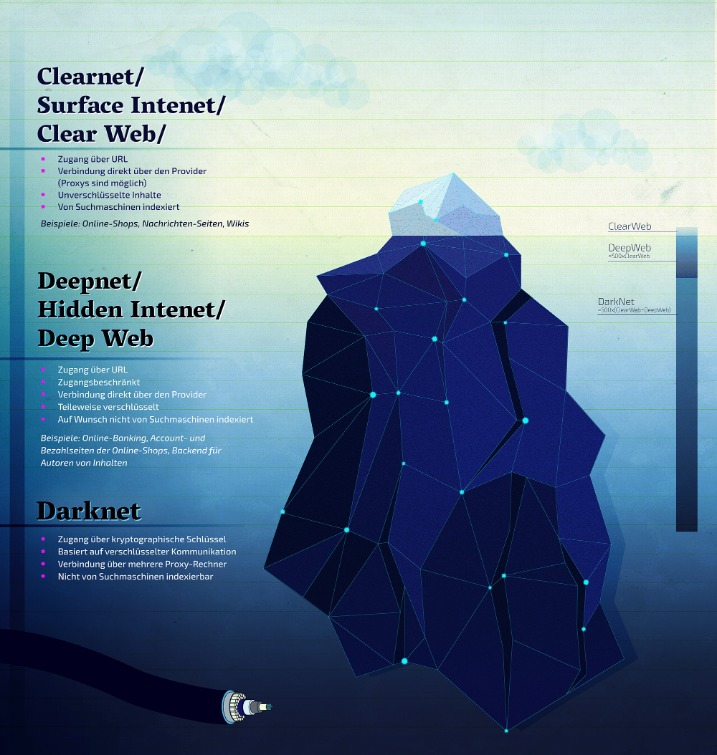
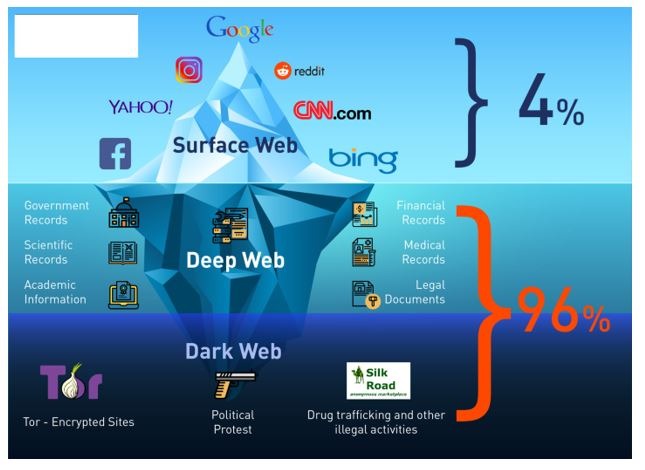
Users slip into this shadowy realm using a anonymizing browser, like Tor (The Onion Ring) browser, and a Virtual Private Network (VPN) to protect their identity and secure their connection. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It is easily accessible by the general public and requires no special configuration.
Why Our Site Is Better: Up-to-Date, Secure, And No Tracking
Vice City listens to the problems faced by its customers and vendors and solves them so that they can keep using the platform with ease. To access the marketplace, dark web users must register first and pass the CAPTCHA test to prove they are human. The site allows users to find and buy a vast variety of products and services.

Hidden Wiki Is A Good Choice For Darknet Users
The search engine doesn’t impose censorship, meaning you can find a broad spectrum of sites, including those that may be illegal or disturbing. You can conduct discussions about current events anonymously on Intel Exchange. There are several whistleblower sites, including a dark web version of Wikileaks. Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there. While the Tor Browser provides strong anonymity, using a VPN (Virtual Private Network) alongside it adds an extra layer of security and privacy.
The Hidden Wiki is a comprehensive starting point for exploring verified dark web links. Unlike many imitators, this is the official Hidden Wiki that maintains a curated directory of legitimate .onion services. During my testing, I found its categorized index particularly helpful for discovering trustworthy sites across various topics. All the dark web websites we’ve listed in this article will not be of much use to you unless you know how to access and use the dark web.
Saved Searches
The best thing is to actually understand how to find the fresh, new links. While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events.
The looming threat of quantum computing has sparked adoption of post‑quantum cryptography in anonymity networks. The Tor Project began experimenting with hybrid algorithms in 2024, and I2P is exploring lattice‑based schemes for secure routing. These safeguards aim to future‑proof traffic from potential decryption by quantum‑enabled adversaries. AlphaBay debuted in September 2014 and quickly eclipsed Silk Road’s record, amassing more than 200,000 users, 40,000 vendors and 250,000 illicit listings.
What To Do If You See Something Illegal
- Alongside pills and powders, sellers offer passports, driver’s licenses and Social Security numbers—often bundled with “fullz” (complete identity profiles).
- By using .onion email providers, you not only align with the privacy-oriented ethos of Tor but also enhance your overall online security.
- However, note that Dark.fail monitors site uptime status and cannot tell whether the site is safe.
- Instead of standard URLs, it uses non‑indexed domains like “.onion” and routes every connection through multiple encrypted relays to mask both server and user identities.
- In this sequel, I’m going to show you some of the not-so-clear-web’s hidden Easter eggs and how to get there.
- But as long as you don’t knowingly engage in illicit activity on the dark web, you are completely fine.
A robust antivirus can help block malware and other online threats, even on the dark web. Stay safe and informed as you explore the deeper layers of the internet. Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. There’s a reason why this onion website is called the Imperial Library; with over downloadable 500,000 books and articles, this may be one of the largest digital libraries, period.
- Although the social application is known for collecting data on its platform, it does not like sharing the information with others.
- Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection.
- Reports and discussions about red rooms are mostly rooted in myth and sensationalism fueled by the anonymity of the internet.
- Following these precautions will help you explore the Hidden Wiki and the dark web with greater safety and confidence.
At the heart of our mission is a commitment to providing users with verified, up-to-date, and safe onion directories to help navigate the dark web responsibly. The Hidden Wiki and its alternatives offer valuable gateways to deep web content that isn’t accessible through conventional search engines. However, the dark web environment can be unpredictable and sometimes dangerous, filled with scam links, phishing sites, and other malicious threats. That is why we emphasize caution, vigilance, and adherence to best security practices when exploring these hidden corners of the internet.
Scam Links, Phishing Clones, And Honeypots On The Hidden Wiki
Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Archive.today collects snapshots of websites and archives them for later viewing. If this sounds similar to The Wayback Machine, the concept is indeed the same. However, The Wayback Machine allows website owners to block their sites from being archived, while archive.today does not.
Security And Practical Recommendations
What’s more, you should always use a VPN (like ExpressVPN) with Tor to protect yourself from IP leaks. I also recommend using an antivirus (like Norton 360) to protect your device from malware infections. Its free plan comes with up to 1 GB of storage, 150 messages per day, and 1 email address.
Does The CIA Have An Onion Site?
It brings in vendor reviews from other places and verifies them using PGP signatures, so buyers can feel a bit more confident about who they’re dealing with. There’s also a premium account option for users who want extra benefits. And when it comes to paying, the site sticks to Bitcoin (BTC) and Monero (XMR) to keep transactions private. Understandably, as in the case with most illicit trade markets, you don’t even need to verify your email Awazon.
It also includes any content that its owners have blocked web crawlers from indexing. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. While you’re at it, now might be a good time to check whether any of your personal information has been leaked on the dark web.



