Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
Dark Net Drug Markets Kept Alive By Great Customer Service
Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Taking the necessary precautions makes tracing your activities on the dark web difficult. For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. However, most are outdated and have not kept up with the changing landscape.
Opioid Painkillers
That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide. This just involves turning on your VPN before you open Tor and connect to dark web sites. Pastebins are text sharing services, useful for sending and sharing large snippets of code or text.
D Onion Websites: Between Anonymity And Risks

Since then, she has worked across various settings including outpatient, inpatient, and community corrections programs. Hailing from Boulder County, Courtney embarked on her academic journey by earning a bachelor’s degree in psychology. She furthered her education by completing a master’s of science in clinical mental health counseling from Capella University. Additionally, Courtney obtained certificates in Alcohol and Drug Studies and is certified in Branspotting, a clinical treatment technique aiding individuals in processing trauma.
Microsoft Strengthens Security After China-Linked Attacks
Quercetin also decreases elevated blood pressure and cardiac hypertrophy (165). Furthermore, quercetin prevents atherosclerosis by inhibiting lipid peroxidation (167). S-alk(en)yl cysteine sulfoxide, another component of onion, has been shown to reduce serum LDL cholesterol, protect LDL cholesterol from oxidation and raise high-density lipoproteins (HDL) cholesterol ( ). Moreover, some studies have demonstrated that S-methyl cysteine sulfoxide isolated from onion possesses anti-oxidative and hypolipidemia properties ( ).
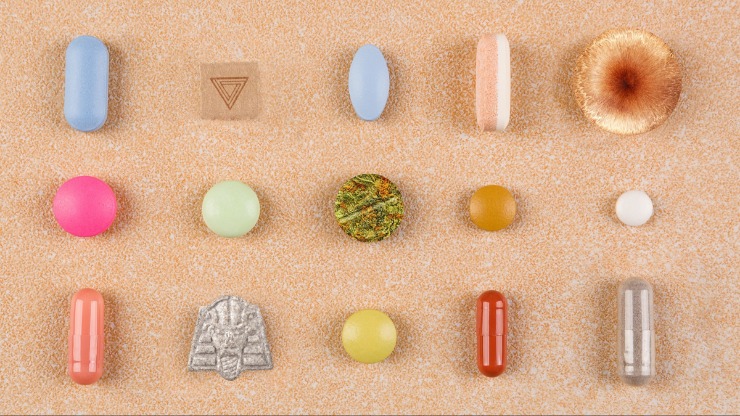
Download Drugs And The Darknet

If 2/3 multisig is used, at least 2 of these 3 parties must sign a transaction. Exit-scams are not possible if the market is not holding any funds in user accounts. These are markets which do not have or use “in-built wallets for each account”. Meaning, buyers can pay for each order directly from their external, third-party wallets. This is one of the oldest and most well-established single vendor markets on this list. Because there’s no “commission” that the vendor pays, the prices here are cheaper than multi-vendor markets.

These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers. Keep in mind that visiting the dark web isn’t illegal, but engaging in criminal activity there is. Even after Silk Road went down, dark web marketplaces haven’t slowed down. Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. After that, many other marketplaces kept trying to take its place and become the top dark web market.
Trending Darknet Sites
You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together.
Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with. Also, you can set a strong password to protect your message and choose how long it will take to expire.
- These tools scan dark web forums and marketplaces for any signs of your compromised credentials.
- Law enforcers can use custom software to infiltrate the dark web and analyze activities.
- They’re tightening security and carefully screening anyone who wants to join.
- It has a bidding feature, with new batches of stolen data being frequently added.
Onion has been indicated to reduce food transit time in the gastrointestinal tract (174). Some studies have also shown that this plant stimulates the growth of useful microorganisms such as bifidobacteria and lactobacilli in the colon due to its high soluble fiber content, including inulin and fructooligosaccharides (40, 175). In addition, it has been reported that flavonoids (e.g. quercetin) content in onion has anti-spasmodic and anti-diarrheal activities (176). Moreover, quercetin appears to have a therapeutic potential in treating peptic ulcers by promoting mucus secretion and the inhibitory effect on Helicobacter pylori growth (177, 178). Administration of 1.5, 02 and 2.5 g/kg of onion powder to chicks led to increased weight gain and feed consumption.
Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. Before your data reaches a site, Tor encrypts your connection and redirects it through a series of servers called “nodes” or “relays” to replace your IP address with each server’s address until it reaches the website. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google.
Vendor Voice
Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there.
Money Laundering
In particular, in the semantic comparison model, the size of the input layer was doubled while not expanding either the hidden or the output layer. Hence, every word has 2 vectors, each describing the word’s relations with other words in one corpus. In the meantime, these 2 vectors are still comparable because they are used together in the neural network to train a single skip-gram model for predicting the surrounding windows of context words. The Hidden Wiki is a longstanding directory of dark web sites that offers a way to browse onion services. It’s been around for many years and helps users navigate the dark web by curating links to various resources.
Darknet Drug Markets
Some marketplace operators first build trust by running a legitimate platform. The fallout for victims whose data is stolen and sold can be devastating. They suffer losses such as identity theft, financial loss, and emotional distress due to damage to their personal and professional lives. They really don’t care about the loss and dilemma of the victims whose data has been stolen.
Individuals suffering from substance abuse often hide their habits by using slang to refer to specific substances. In a very practical way, this is their own real language, and they use it as they seek, purchase, and use drugs. Parsarad is charged with conspiracy to distribute controlled substances and distribution of controlled substances in the Northern District of Ohio and elsewhere. Nemesis users were not allowed to conduct transactions in official, government-backed currencies.