I am not suggesting that you do this manually; this is a situation in which a little automation goes a long way. In fact, this is a situation in which looking around for a good tool might be appropriate. To find the best solution, we should first answer ‘why do we want to enumerate all supported ciphers?
Hydra Darknet Market
- Customers need only a username and password to register, while vendors have to pay a $75 vendor bond or show a Recon profile with at least 20 sales.
- BOTs read exposed ‘mailto’ Email IDs and spam individuals’ inboxes.At certain level, this module helps in overcoming email-spamming issue by exposing encrypted ‘mailto’ Email IDs to the BOTs.
- The Cypher Manual aims to be as instructive as possible to readers from a variety of backgrounds and professions, such as developers, administrators, and academic researchers.
- Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud.
- This is why it is one of the best go-to tools for data scientists and anyone who ventures into the unknown with a tight schedule on ROI.
You can still control some parameters like tags, page size and page-number though. Simple privacy-focused links – Share links without displaying or storing any personal data within your data processors. This is why it is one of the best go-to tools for data scientists and anyone who ventures into the unknown with a tight schedule on ROI. However, there are some syntax best practices that are highly recommended by the community, which help with consistency and makes reading the query easier. Omitting the relationship direction is less efficient, but will return data where either relationship direction exists.
Click below to get your free copy of O’Reilly’s Graph Databases ebook and start building better apps powered by graph technologies. I encourage you to try it with your favorite web-APIs and send us your example with graph model, Cypher import query and 2-3 use-case queries that reveal some interesting insights into the data you ingested to Neo4j’s query language Cypher supports loading data from CSV directly but not from JSON files or URLs. This cypher url aggregator has completely transformed my shopping experience.
- Our mission is to simplify navigation in the complex and evolving world of the darknet.
- We recognize that the true value of exceptional cypher url lies in the unique stories, craftsmanship, and personalized experiences that they offer.
- Be aware that since the filter inside WHERE can contain any kind of an expression, the expression can be so complicated that the index doesn’t get used.
- When curl connects to a TLS server, it negotiates how to speak the protocoland that negotiation involves several parameters and variables that bothparties need to agree to.
- As we continue to push the boundaries of what’s possible, you can trust that our platform will be your gateway to the future of exceptional cypher darknet shopping.
Parsing, AST and semantic analysis for the Cypher cypher market Query Language openCypher Public. Cypher, a Solana-based DeFi protocol, took in funding from Sino Global finance opportunities to decentralized finance (DeFi) markets. The Cypher pattern forex appears less frequent than other harmonic patterns. Buy and sell Dota 2 items on the Steam Community Market for Steam Wallet funds.
List Ciphers Supported By An IMAP Server
Users can simply express what data to retrieve while the underlying engine completes the task – eliminating the need for technical implementation knowledge. You can deconstruct maps with dot notation map.key and arrays with slices array0..4. You’d use UNWIND to convert collections into rows and FOREACH to iterate over a collection with update statements. To create nodes and relationships we use MERGE and CREATE commands.

Embrace The Future Of Cypher Url With Our Innovative Platform
One tool I haven’t seen mentioned in other answers is Stephen Bradshaw’s SSLTest, which, among other things, is intended to compare “the detected ciphers and protocols against compliance standards such as DSD ISM and PCI-DSS.” There is no better or faster way to get a list of available ciphers from a network service. Plus, nmap will provide a strength rating of strong, weak, or unknown for each available cipher. The following is an example of how you can connect to a Neo4j DBMS in read mode and then change the access mode to write in the interactive shell.
Create A Label-property Index
One of the benefits of graph databases is that you can store information about how elements (nodes) are related to each other in the form of relationships. The source file books.csv contains information about both authors and books.From a graph perspective, these are nodes with different labels, so it takes different queries to load them. Data from relational databases may consist of one or multiple CSV files, depending on the source database structure.A performant approach is to run multiple passes of LOAD CSV to import nodes separately from relationships. This notebook shows how to use LLMs to provide a natural language interface to a graph database you can query with the Cypher query language.
Neo4j – Construct A Cypher Query Through Url
From cutting-edge technology to premium lifestyle products, our curated selection ensures you have access to the latest and greatest. Elevate your cypher website game with our unique offerings, designed to enhance your overall shopping journey. Experience the difference a truly exceptional marketplace can make, and let us be your guide to the world of the best cypher website and cypher tor. As we look to the future, we’re excited to integrate cutting-edge augmented reality (AR) technology into our cypher url marketplace.
Almost every site offers some kind of API or endpoint that returns JSON and we can also query many NOSQL databases via HTTP and get JSON responses back. This query returns the average, maximum, and minimum age of all nodes with the label “Person”. By using the Qury API, you will protect sensitive data at scale while still being able to access it as well as tracking it in your analytics platform like any other link. The ability to completely redesign how the data is connected AFTER loading up all the data is incredibly helpful.
The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. To optimize queries that fetch nodes with a certain label and property combination, you need to create a label-property index. For the best performance, create indexes on properties containing unique integer values. Cypher differentiates itself with an uncluttered yet dynamic approach.
Cypher Syntax
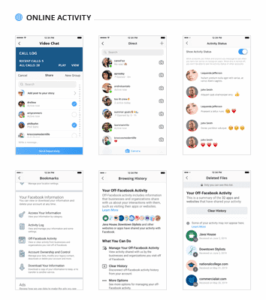
H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Generate secure links for recipients to decode messages using the same encryption key.
Issues For Cypher Link
Cypher’s main advantage is simplicity for sellers and buyers alike. It doesn’t require previous dark web experience, extensive knowledge, or serious investments to sign in. Customers need only a username and password to register, while vendors have to pay a $75 vendor bond or show a Recon profile with at least 20 sales.

Connection Scenarios
If I understand correctly, I can “pre-populate” my connection settings like e.g. user but I cannot directlyestablish the connection with one URL. Due to its illegal nature, the dark web trading industry can be as ruthless as the jungle. There is no wonder that some darknet marketplaces prefer to behave like chameleons and blend in. This query will search the whole graph for weakly connected components. This query will make sure that every node with the label City has the property name.
Conventions for property names and node/relationship alias typically depend on the framework in which you are using the queries. In Python, the usage of snake_case for these is more common whereas in NodeJS camelCase would be the norm. In SQL when joining two tables, very common joins are LEFT/RIGHT joins which define the result set you are seeking. In Neo4j Cypher relationship directions is all about pattern matching. Variables can be used for relationships in the same way as for nodes.Once you specify a variable, you can use it later in the query to reference the relationship. In Cypher, relationships are represented as square brackets and an arrow connecting two nodes (e.g. (Node1)-→(Node2)).
Cypher boldly expands its product categories beyond the usual, covering areas like drugs, fraud, hacking, counterfeits, and even defense/intelligence, each with detailed subcategories. Popular items such as cannabis and stimulants are available, but the market shines in its ‘Other’ fraud section, offering unique guides and tools. Cypher also stands out for exclusive offerings like custom hacking services, malware, and sought-after data dumps, reinforcing its status as a trailblazer in the darknet market arena. Neo4j Browser is an easy way to access a Neo4j database.To establish a connection, select connection protocol, enter the connection URL, and the user credentials. The translator supports multiple popular encoding methods including Caesar cipher, Vigenère cipher, and substitution ciphers. You can create custom letter-to-letter mappings, use numeric codes, or implement symbol substitutions.