However, it’s much harder to get at the people who are doing the uploading and downloading. DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web. Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions.
PRIVACY ALERT: Websites You Visit Can See These Details About You:
I will be providing updates as fast as I can and there are many more sleepless nights ahead for me as I prepare for a large influx of users. I will be trying to get new fixes and features live tonight and tomorrow as well as expanding the site-wide moderation team. Simply put, onion sites are websites that are hosted on the Tor darknet that use the “.onion” top-level domain instead of “.com,” or “.gov” for example. All Onion sites use The Onion Router (Tor) protocol to encrypt the user’s connections. It’s only possible to access onion sites through the Tor browser or by setting up some special network configurations.
独家:暗网市场Abacaus Market无法访问,似乎正在进行退出骗局
With a refined interface, strict quality standards, and support for multiple cryptocurrencies, Crown positions itself as a platform of excellence and trust. Focused on reliability and discretion, Crown has quickly become a favored destination for darknet users seeking sophistication and stability. Anubis is a darknet marketplace cloaked in symbolism and built for those who value security, legacy, and control.
What Is The Dark Web? How To Access It And What You’ll Find
Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk. This is because law enforcement often actively monitors these sites. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential.
- This traditional search engine is also compatible with the dark web and can help you find dark web websites.
- TorZon is a well-known name in the darknet landscape, recognized for its streamlined marketplace experience and long-standing presence in the community.
- Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences.
- Pharoah is centralizing the darknet to a scale that previous darknet market admins have only dreamed of.
- However, it’s much harder to get at the people who are doing the uploading and downloading.
As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. Other sites explicitly block search engines from identifying them. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship.
Saved Searches
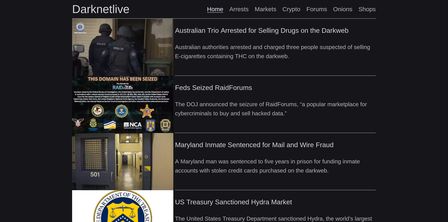
{It also includes any content that its owners have blocked web crawlers from indexing. Darknetlivereport.com is an independent research network run by anonymous journalists that specializes in the latest news, unbiased articles and assessment of hidden services. EXch was a service operating since 2014 that primarily accepted Bitcoin of criminal origin. The service allowed users to exchange various cryptocurrencies for other cryptocurrencies ( so-called swapping). The platform advertised anonymity for its users, meaning they would not have to verify their identity and user data would not be stored.}