The toFloatOrNull() function converts an INTEGER, FLOAT or a STRING value to a FLOAT.For any other input value, null will be returned. The toBooleanOrNull() function converts a STRING, INTEGER or BOOLEAN value to a BOOLEAN value.For any other input value, null will be returned. The function startNode() function returns the start NODE of a RELATIONSHIP. The nullIf() function returns null if the two given parameters are equivalent, otherwise it returns the value of the first parameter. The endNode() function returns the the end NODE of a RELATIONSHIP. The coalesce() function returns the first given non-null argument.

How To Prepare For Unexpected Challenges In Cypher?
Optionally CALL a subquery.Similar to OPTIONAL MATCH, any empty rows produced by the OPTIONAL CALL will return null and not affect the remainder of the subquery evaluation. A CALL subquery is executed once for each row.In this example, the CALL subquery executes three times. List all procedures that can be executed by the current user and return only the name of the procedures. LIMIT constrains the number of returned rows.It can be used in conjunction with ORDER BY and SKIP. If a write clause is followed by a read clause, WITH must be used as a separator between the two. WITH cannot de-scope variables imported to a CALL subquery, because variables imported to a subquery are considered global to its inner scope.
The ceil() function returns the smallest FLOAT that is greater than or equal to the given number and equal to an INTEGER. The abs() function returns the absolute value of the given number. The percentileDisc() function returns the percentile of the given value over a group, with a percentile from 0.0 to 1.0.It uses a rounding method and calculates the nearest value to the percentile.
- The OR operator is used to combine multiple boolean expressions, returning true if at least one of the conditions is true.
- Grant SHOW TRANSACTION privilege to list transactions by the specified users on home database to the specified roles.
- The localdatetime.truncate() function truncates the given temporal value to a LOCAL DATETIME instant using the specified unit.
- Grant SHOW INDEX privilege to list indexes on all databases to the specified role.
- Prioritize identifying any entry points like login pages or exposed APIs, which may require a password.
This example sets the property marked to true on all relationships along a path. The ANY keyword can be used to test the reachability of nodes from a given node(s). It returns the same as SHORTEST 1, but by using the ANY keyword the intent of the query is clearer.
Caesar Shift Messages
Standalone call to the procedure db.labels to list all labels used in the database. Note that required procedure arguments are given explicitly in brackets after the procedure name. SHORTEST k finds the shortest path(s) (by number of hops) between nodes, where k is the number of paths to match.
Ready To Strengthen Your Security?

You can of course break up a larger pattern into smaller ones, and use MERGE on the smaller patterns if needed, when there’s a possibility that a part of this linked pattern already exists. While there is a matching unique Person node with the name Oliver Stone, there is also another unique Person node with the role of Gordon Gekko and MERGE fails to match. While there is a matching unique Person node with the name Michael Douglas, there is no unique node with the role of Gordon Gekko and MERGE, therefore, fails to match. Similar to MATCH, MERGE can match multiple occurrences of a pattern.If there are multiple matches, they will all be passed on to later stages of the query. While this suggests an increasing cybercrime threat in the region, the use of local languages and dialects may also assist law enforcement with pinpointing the location or origin of darknet users.
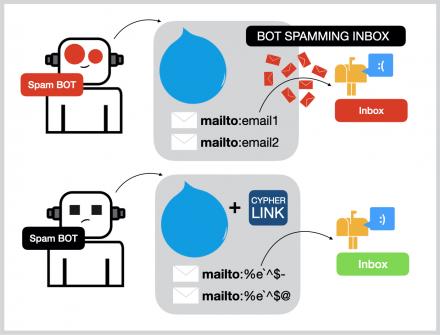
LIST NOT NULL value. To conquer Cypher challenges, common tools like Nmap, Dirb, and Nikto are essential for reconnaissance, especially when you want to download necessary data such as source code from the default directories. These tools aid in identifying command injection vulnerabilities and services on targets, crucial for success in the HackTheBox environment. As a pioneering and bold venture in the darknet realm, Cypher Market offers an extensive range of products and services, pushing beyond the limits of typical internet marketplaces.
Takes an integer as the order, then returns the prime in the order.Useful for generating large primes by just inputting their order.Default argument is a random 8-bit number plus one, in case 0 ischoosen. We read every piece of feedback, and take your input very seriously. The neo4jShell.bat file has been removed since this question was asked. The new approach to execute cypher files is to use the web application called LazyWebCypher .
Market PGP Key
The toString() function converts an INTEGER, FLOAT, BOOLEAN, STRING, POINT, DURATION, DATE, ZONED TIME, LOCAL TIME, LOCAL DATETIME or ZONED DATETIME value to a STRING. The toInteger() function converts a BOOLEAN, INTEGER, FLOAT or a STRING value to an INTEGER value. The toFloat() function converts an INTEGER, FLOAT or a STRING value to a FLOAT. The toBoolean() function converts a STRING, INTEGER or BOOLEAN value to a BOOLEAN value. The haversin() function converts half the versine of a number.
Identifying Target Services And Ports
Cypher challenges on HackTheBox test your skills in cryptography and cybersecurity. These challenges often involve deciphering encrypted messages or identifying vulnerabilities in a given cipher. By mastering these challenges, you enhance your understanding of encryption techniques and their real-world applications. Successfully completing Cypher challenges can significantly boost your confidence and problem-solving abilities in the field of cybersecurity, making you a more proficient and versatile ethical hacker. Embrace the opportunity to sharpen your cryptography skills and dive into the intriguing world of Cypher challenges.
ON DATABASE – INDEX MANAGEMENT Privileges
LIST NOT NULL value.
Note that the privileges for starting and stopping all databases, and transaction management, are not included. Deny CREATE privilege on all nodes with a specified label in all graphs to the specified role. To remove a granted or denied privilege, prepend the privilege query with REVOKE and replace the TO with FROM. List all roles that are assigned to at least one user in the system, and the users assigned to those roles. List all database aliases in Neo4j DBMS and information about them.

In our continued effort to push the boundaries of the cypher url marketplace, we’re thrilled to announce our integration of blockchain technology. By leveraging the power of decentralized ledgers, we’re able to provide our customers with an unprecedented level of security, transparency, and efficiency when it comes to their cypher tor transactions. Say goodbye to the limitations of traditional payment methods and hello to the future of cypher tor with our blockchain-powered platform. Experience the seamless, secure, and lightning-fast transactions that will redefine the way you think about cypher darknet shopping.
The password for the page can be discovered in Question #7note 2 from “The One True Intelligence Test”. Eckleburg, an optometrist from The Great Gatsby who is mentioned in a passage from that book included as “required reading” in The Book of Bill. Grant ASSIGN PRIVILEGE privilege, allows the specified role to assign privileges for roles. Grant DROP ALIAS privilege to delete aliases to the specified role.
The toFloatList() converts a LIST of values and returns a LIST.If any values are not convertible to FLOAT they will be null in the LIST returned. The toBooleanList() converts a LIST and returns a LIST.If any values are not convertible to BOOLEAN they will be null in the LIST returned. To dynamically access a MAP value, use the subscript operator, .The key can be provided by a variable or a parameter.
We are holding our third cypher market cloud startup showcase on Sept. Torrez Market was established in February 2020, making it a fairly novel darknet market. Grant ALTER DATABASE privilege to alter standard databases the specified role.