
The fallout for victims whose data is stolen and sold can be devastating. They suffer losses such as identity theft, financial loss, and emotional distress due to damage to their personal and professional lives. They really don’t care about the loss and dilemma of the victims whose data has been stolen. While hiring a hacker might sound like something out of a movie, it’s a very real threat. Businesses may use these services to sabotage their competitors, while individuals may seek revenge or simply want access to private information about someone. The site gives out free samples of the stolen data every now and then to gain more customers.
Traders cash in on stolen credit card data dumps, initial access points to vulnerable systems, credentials, and intellectual property belonging to companies compromised during cyberattacks. Founded in 2005, Exploit.in is one of the oldest Russian-language dark web forums still in operation. This platform connects cybercriminals involved in fraud, hacking, and RaaS deals. With tight access controls and a preference for Russian speakers, Exploit.in maintains a high signal-to-noise ratio, ensuring only serious actors thrive. With over 15 billion records sourced from nearly 936 datasets, BreachForums remains one of the largest dark web forums for data leaks.
Which Is The Best Laptop For Cyber Security Course?
Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet.
Social Engineering – Part 3 What Are The Best Social Engineering Co
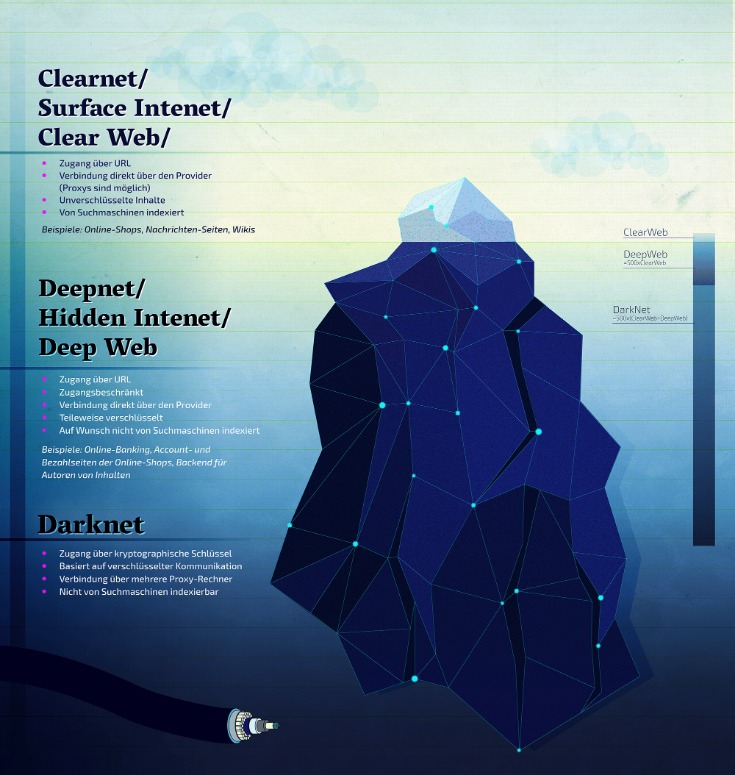
Their dark web presence also creates a secure platform for whistleblowers to submit material without the risk of retaliation. Sci-Hub has nothing to do with science-fiction literature, but with science itself. The first website on our list is, allegedly, the largest repositories of scientific papers on the dark web. Careful though, because many ‘users’ reported malicious links and redirects while perusing Sci-Hub. To access onion sites, users need a stable internet connection and the Tor browser. Taking the necessary precautions makes tracing your activities on the dark web difficult.

What Do People Sell Or Exchange On Darknet Markets?
- It also always uses a secure HTTPS connection, so you’re safer on public Wi-Fi networks too.
- Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks.
- Always use a fake name and a temporary email address when you buy something from the dark net shops.
- Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website.
However, engaging in illegal activities on the dark web is strictly prohibited. OSINT professionals use the dark web to gather intelligence from hidden forums, marketplaces, and databases that provide early indicators of cyber threats and leaks. Security solutions like anti-virus software protect your system and network from malware and other threats. The dark web, being a hub for criminal activities like identity theft and malware distribution, exposes you to various security threats like malware or phishing.
Dark Web Links For Information Resources
The significance is in safeguarding the right to free speech and the role of the press as watchdogs. Businesses should be aware of the potential for data leaks and invest in data loss prevention measures. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. Its affordability and reliability have earned it a loyal customer base. The platform’s activity has increased significantly over the past year, indicating its growing influence and market share in the underground economy. Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data.
What Are The Best Onion Sites?

This traditional search engine is also compatible with the dark web and can help you find dark web websites. We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said. Dark web websites look pretty much like any other site, but there are important differences.
- There is no need to visit darknet marketplaces yourself to know whether your data was leaked.
- Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved.
- Known for its massive index and premium version, Haystak is favored by cybersecurity professionals and threat analysts for its depth.
- Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble.
From its inception, Ahmia has been committed to ethical principles, filtering out content related to child pornography and maintaining a blacklist to mitigate abusive services. This commitment underlines the search engine’s dedication to providing a safe and constructive environment for dark web exploration. That is why in 2006 they created “the most private search engine in the world”, which does not record, track, or share your personal data. Over the years, they added many additional privacy features, such as “Anonymous View” for added protection. They are located in Europe, where privacy laws are among the strictest in the world. However, not Evil is not a repository for illegal services and illegal material.

ProPublica is a non-profit, Pulitzer Prize-winning news outlet that focuses on abuses of power and issues of public trust. ProPublica’s investigative journalism can upset powerful interests, so the outlet joined the dark web to help their journalists and readers access their content anonymously. Being on the dark web also lets whistleblowers send material to ProPublica without fear of reprisal. While you’re at it, now might be a good time to check whether any of your personal information has been leaked on the dark web.
Frequently Asked Questions (FAQs) About The Top 10 Dark Web Search Engines
Using a virtual private network (VPN) masks your real IP by routing your internet traffic through a secure server, making it appear as though you’re browsing from a different location. A VPN also encrypts your connection, keeping your data safe from surveillance and unauthorized access. While they make accessing Tor-hidden websites easier without the Tor browser, they can compromise your privacy and security by acting as intermediaries that might expose your data.
Don’t Provide Personal Information
Law enforcement regularly shuts down these markets, but new ones continuously emerge. Torch is one of the more established dark web search engines, designed to help users navigate the Tor network and discover onion sites. Unlike traditional search engines like Google or DuckDuckGo, Torch indexes hidden websites that operate beyond the reach of the surface web.

Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily. That means that Google wants to minimize the amount of time users spend searching for certain queries. Did you know that Google only shows you a glimpse of all the websites that actually exist?
From Flickr to Facebook posthaste – that would be an accurate description of Dark Lair, an image hosting platform turned social media. Dark Lair allows you to post comments, share music, upload photos, message your dark web ‘friends’, and everything in between. Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online.
Specialized Data Repositories
The second category consists of data stores, which specialize in stolen information. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails.



