The goal is simple — make financial fraud easy and get as much attention as possible. Unlike surface web platforms, darknet markets have no reliable way to verify vendors. Many “trusted” sellers use fake reviews or steal reputations from shutdown markets. Doing so makes it easy to fall into traps set by scammers.
Since its inception in 1992, the task force has been responsible for the seizure of approximately $600 million and more than 2100 arrests. In stepped Empire Market which appeared in February 2018 (about 6-7 months after the demise of AlphaBay/Hansa) and soon became the leader of the Western darknet market ecosystem. The fact that its graphical user interface was built to resemble that of AlphaBay was purposely done to instill a sense of familiarity for users who had become accustomed to AlphaBay. Be wary of any new marketplaces popping up on the dark web.
West Documents
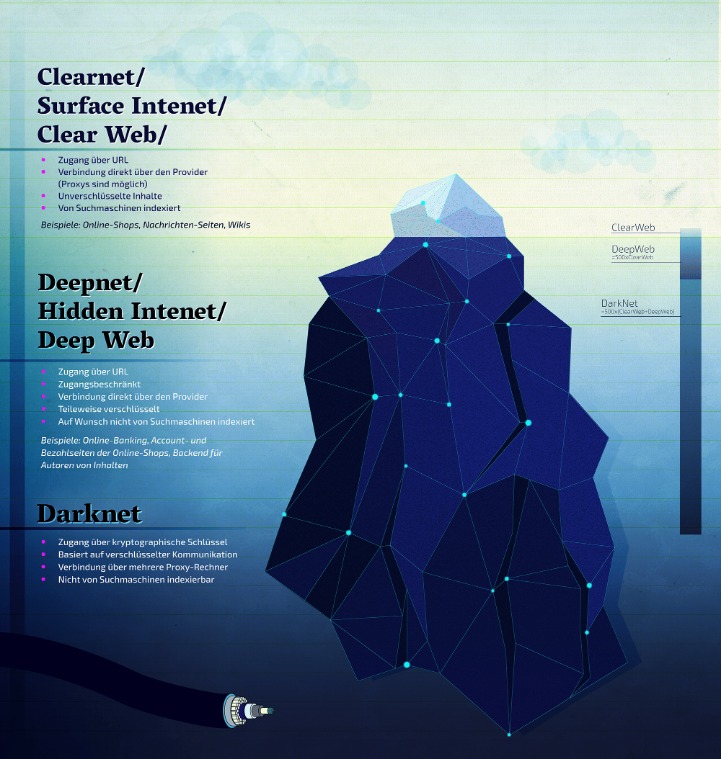
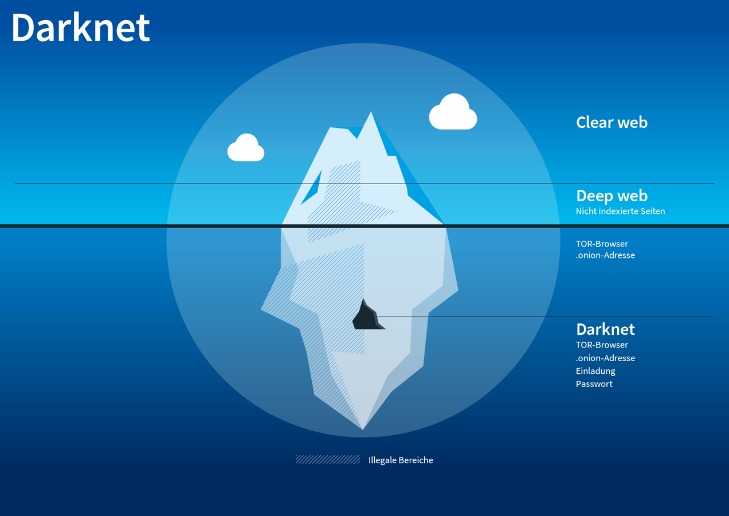
Those who access the dark web do so via the Tor (The Onion Router) browser. The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine).

The Latest Challenge: Expert Forged ID Documents Available For Very Little Money
The Dark Market Sites were designed to facilitate the illicit commerce hosted on the sites by providing anonymity to their users, in at least two ways. First, the Dark Market Sites were only accessible to users of the Tor anonymizing network. Second, the Dark Market Sites accepted payments for their illicit goods and services in “Bitcoin” or similar electronic currency designed to be as anonymous as cash.
Offered categories are drugs and chemicals, counterfeit items, digital products, fraud, guides & tutorials, jewels & gold, carded items, software & malware, security & hosting, services and other listings. Significant technological innovations and trends have reshaped dark-web marketplaces over recent years. In 2025, many platforms have adopted decentralized architectures, reducing single points of failure that previously made them vulnerable to law enforcement takedowns. Users trumpeted Empire as a “solid’ platform” with a great developer team. The darknet market was a classic escrow marketplace (i.e. users deposited funds into Empire and, only then, were able to make purchases).
What Can Criminals Do With Stolen Identity Data?
I’ve poked around; it’s not overwhelming, just a tight selection that works—think curated over chaotic. If you’re into a darknet market with a community pulse and solid uptime, Bohemia Dark Market’s climbing the ranks—give it a spin if you like a vibe that’s less corporate, more crew. Transactions in these underground markets prioritize anonymity and security to evade detection. Payments are typically made using cryptocurrencies like Bitcoin or Monero, which obscure financial trails. Sellers often use PGP (Pretty Good Privacy) encryption to secure communications and protect user identities.

Here’s What Your Data Sells For On The Dark Web
The dark web hosts a variety of illegal activities, many of which fuel cybercrime and real-world harm. Even passive activity on these sites can contribute to criminal networks. For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails.
- You can see all the product categories the marketplace deals with on the homepage.
- Deep learning tools can generate high-resolution facial composites and falsified document templates, complete with authentic-looking fonts, holograms, barcodes, and microtext.
- Despite these challenges, law enforcement agencies continue their efforts to uncover networks, identify perpetrators and curb trafficking.
- The dark web market changes all the time, but some dark web marketplaces have made a name for themselves as the biggest and busiest spots.
- In short, they are offering financial services since 1996 in Tor network and have 13000+ happy customers worldwide.
Tor Stuff

The layers of encryption hide your data and activity from snooping eyes. The FBI is the lead federal agency tasked with combating cybercrime, but the agency told Spotlight they could not accommodate our request for interview about what they’re doing to fight illegal activity on the dark web. Talcove says the biggest obstacle that law enforcement faces in fighting fraud on the dark web is just how massive it is, often used by transnational criminal organizations to carry out fraud. David Hollingworth has been writing about technology for over 20 years, and has worked for a range of print and online titles in his career. He is enjoying getting to grips with cyber security, especially when it lets him talk about Lego. Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved.
It offers outstanding privacy features and there is currently a discounted rate available through this link. As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web.
Gadgets Dark Web Links
I’ve used it; shipping’s discreet—plain packages or DeadDrops—and uptime’s been flawless, rivaling Abacus. It’s not as community-driven as Bohemia, but the polish makes up for it—feels like a pro operation, not a fly-by-night deal. If you’re after a darknet market with variety and a forward-thinking edge, Tor2door Market’s a contender—watch it close in 2025 as that AI kicks in. Alright, let’s get into the meat of it—the darknet markets that are ruling 2025. I’ve been poking around these places for a while now, from the giants like Abacus to the old-timers like Vice City.
Please read our article How to check if a cryptocurrency site is legit or a scam.. Music makes life better — but only if it’s coming from a safe, legit source. Standard search engines index these websites and are accessible without special configuration. Businesses must prioritize cybersecurity by implementing Dark Web scanning tools, strengthening access controls, and educating employees about emerging threats. Identifying security vulnerabilities before cybercriminals exploit them is essential for maintaining operational integrity.
Fake IDs And Documents On The Dark Web: Where They Come From And The Risks
In addition, the use of cryptocurrencies facilitates anonymous transactions, which further simplifies the trade in stolen data. At the same time, the professionalization of darknet markets has led to a safer and more efficient trading environment. These markets offer user-friendly interfaces and reliable services, further fueling the trade in stolen data. Finally, the growing demand for stolen data used for illegal activities such as identity theft, fraud and phishing is helping to strengthen the market. Darknet markets have allowed cybercriminals, fraudsters and criminals who trade in weapons, drugs and illegal products to trade without much concern of getting caught due to the anonymity provided by the deep-web.
- It was quite popular for selling a wide range of products and services.
- Bitcoin cards can be used for cashing large amounts and shopping.
- To get into DNMs, you’ll likely have to figure out the basics of things like PGP encrypted messages and using the TOR browser.
- One of the things STYX is infamous for is having a rigorous verification process for users that makes it seem more exclusive.
Exposure To Malware And Scams
We don’t stop at making IDs that look real—we go the extra mile to ensure they function like the real thing. Our IDs are equipped with advanced security features that even the sharpest eye can’t detect. From scannable barcodes that work flawlessly in any system to UV ink that lights up under blacklight, we replicate every modern security measure used in official IDs. One of the biggest problems cybersecurity teams face isn’t a lack of tools — it’s too many alerts.
Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services. Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. Nemesis Market is a relatively new wallet-less shop on dark web where you don’t need to deposit any amount in your wallet before buying products from here.