
All content provided is for educational purposes regarding online privacy and security. The closure of Archetyp Market will likely trigger a temporary disruption in darknet drug supply chains, but it won’t end darknet drug trafficking altogether. Other markets will emerge to fill the gap, possibly adopting more sophisticated security measures to avoid detection. Law enforcement agencies worldwide will need to increase their use of AI-driven analytics and cross-border cooperation to stay ahead. The fight against darknet drug markets is entering a new phase where technology and international alliances will be decisive in shaping outcomes.
- Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI.
- Therefore, given the nature of anonymity and privacy of the dark web, several stores keep on emerging in the dark despite a continuous crackdown on several others.
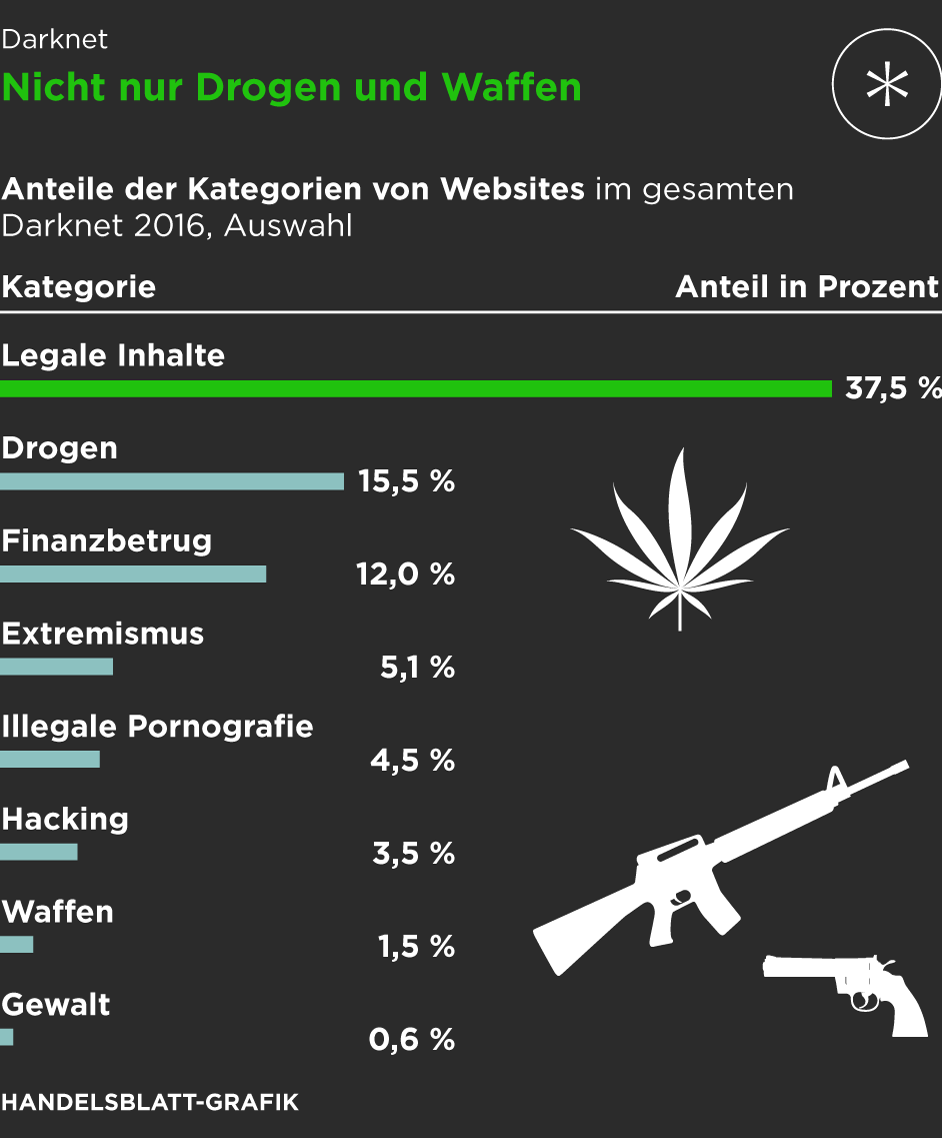
- The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals.
- In summary, the Tor Browser is your gateway to the darknet, providing a secure and anonymous way to explore and access resources that are otherwise hidden from the standard internet user.
- This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity.
Types Of Dark Web Sites (and What Really Goes On There)
Just like Google, the dark web has some search engines present on it. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. Hence, you never know when a popular .onion site is going to vanish, or even die.

Arrest And Trial Of Ross Ulbricht

Downloading files from the Tor browser can compromise your anonymity. Malicious files might bypass Tor’s security, giving away your real IP address. If you must download files, ensure you’re using a separate, secure environment — such as a virtual machine. Updates often include security patches that protect you against vulnerabilities and potential breaches. Thus, what started as an intriguing experiment with anonymity has transformed into a multifaceted realm, serving both the liberation of voices silenced and the shadowed dealings that we pursue. Just like the internet from which it emerged, the dark web reflects a mirror of society’s broader interactions—exposing our greatest fears and our deepest desires within its unseen corridors.
ChromeAlone – Chromium Browser C2 Implant For Red Team Operations
The darknet market ecosystem operates as a complex web of interdependent participants. Each element serves specific functions that collectively maintain the operational integrity of these platforms. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity.
Silk Road And Early Markets
Therefore, you need to take your privacy seriously and start by using strong and unique passwords for every online account you open. According to the United Nations Office on Drugs and Crime (UNODC), all guns are manufactured legally. Therefore, it means that even the guns on the dark web start legally, but along the way from creation to purchasing, a lot of things happen, which makes it easier for the guns to end up on the dark market.
About Archetyp Market – Anonymous XMR-Only Platform
This is where an Onion website, like the Tor browser, comes in handy. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. This article lists some of the best dark web websites you can visit securely. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. Patch notes are provided via the community forum when updates are made to the Archetyp marketplace. A brief rundown of the statistics on Archetyp is very impressive.

Top Darknet Marketplace
Torzon market made its debut in September 2022, and ever since, it has been on an upward trajectory. In fact, it now features more than 11,600 illegal items, which include hacking tools, hard drugs, and all types of cybercrime services. Therefore, it’s clear that as long as there’s demand and supply of illegal products, the darknet markets are going nowhere anytime soon, no matter the number of times law enforcement takes them down. Launched in September 2022, Torzon Market operates on the Tor network and features over 11,600 illegal products, including drugs and hacking tools. It enhances buyer transparency by importing vendor feedback with PGP proof.
Anonymity Through Tor
The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience. Transactions within these marketplaces typically leverage cryptocurrencies—most commonly Monero, Bitcoin, and privacy-centric digital currencies developed specifically to enhance transaction anonymity. Monero, in particular, has become the preferred cryptocurrency on the dark web in 2025 due to its advanced privacy mechanisms, which obscure transaction histories and wallet balances from public view.

You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. Archive.today is considered an important tool to track changes across government and corporate websites, preserve cultural heritage, and keep knowledge outside of autocrats’ reach. You can archive any site you want, or retrieve historical records wherever available. When visiting the dark web, use a secure browser like Tor, do not reveal any of your personal information, and don’t open suspicious files or links to stay safe. Countries differ in how aggressively they monitor Dark Web activity. In some authoritarian states, accessing Tor nodes can flag you for surveillance.
Like ransomware, criminals can buy software and inject your devices with viruses. With it, they can spy on people, steal their sensitive data, or secretly control their devices. These software are also capable of launching DDoS attacks and phishing campaigns. Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment.
Join Our Cyber World:
By keeping these tips in mind and maintaining cautious online behavior, you can safely navigate the depths of the Tor network while ensuring your anonymity. Always stay aware of evolving threats and continue educating yourself about best practices for online privacy. For added security, consider using a reliable VPN in conjunction with Tor. A VPN can mask your Tor usage from your Internet Service Provider (ISP), but be cautious — some VPN providers keep logs that could compromise your anonymity.
With the onion browser, you can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine.
Darknet Communications In 2025 – From IRC Forums To Telegram Crime Networks
Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies.


