Keep an encrypted offline list of updates to maintain access without interruptions. Haystak’s free tier offers basic keyword searches on a limited index with ads and weekly updates, suitable for casual users. The premium version (~$20-50/month) unlocks full access to billions of pages, advanced filters (e.g., regex, date sorting), historical archives, and ad-free UX for in-depth research. They often have smaller indexes (e.g., Ahmia’s ~10,000 sites) and may include ethical filtering to block illegal content, but they lack features like personalized ads or real-time updates. NotEvil emerged in the mid-2010s as a successor to TorSearch, inspired by Google’s “Don’t be evil” motto.
Torlinks: The Curated Directory For Structured Browsing
It’s the process of scanning dark web markets, forums, and .onion sites for specific identifiers, such as email addresses, passwords, or company data. Specialized dark web monitoring services continuously scan the dark and deep web using tools specifically designed for that and extensive indexing methods to look for compromised data. Most dark web search engines rely on these crawlers, but some also utilize manual link submission. It means they search for .onion websites through automated means but also allow users to suggest new sites, most often anonymously.
Encrypted Communication Tools
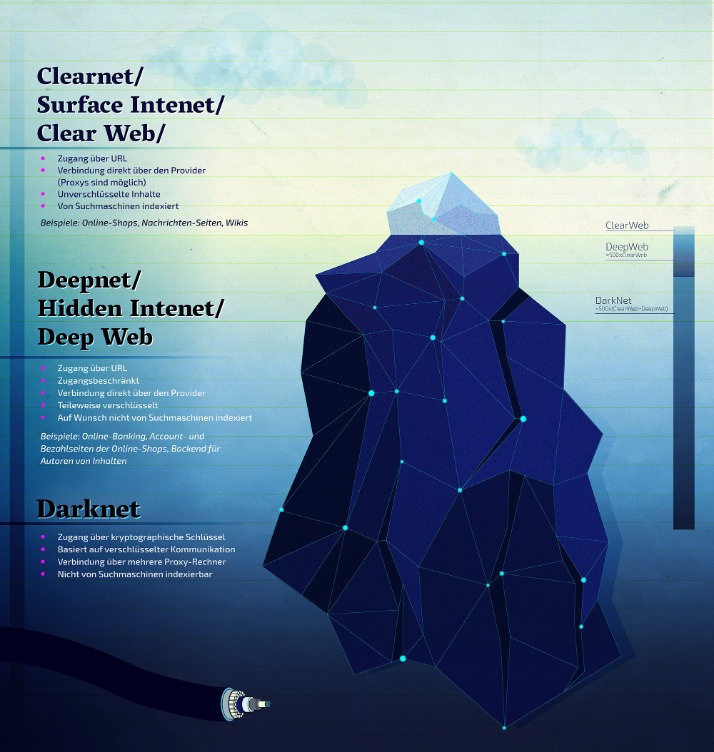
This engine uses information from publicly sourced sites (such as Wikipedia) with the aim of increasing traditional results and improving relevance. Its philosophy emphasizes privacy and not registering user information. Accessing darknet requires using Tor Browser, a special web browser that routes your internet traffic through a global network of relays managed by volunteers. This way, it becomes very difficult to trace which websites you’re visiting, and these sites won’t know where you are located.
DuckDuckGo
While anyone can use it, it’s built for high-stakes exchanges, making it overkill for routine file sharing or data backups. Major news outlets like The New York Times, The Economist, and The Guardian host SecureDrop instances on the dark web to give sources a safe, anonymous way to share sensitive information. Dark web links can change frequently, so always verify addresses from multiple trusted sources before visiting any .onion site. The links shared in this guide were working during testing, but legitimate services occasionally move to new URLs to enhance security. I recommend bookmarking verified links rather than relying on search results. I always cross-reference links from multiple verified sources before visiting any dark web address.
In addition to being one of the best onion search engine, Ahmia also is a search engine for the I2P network if you use or know what that is. Moreover, when accessing the dark web, you’re probably already looking for things which are either illegal, or restricted by the govt. Torch is an onion site, so you’ll need the Tor Browser in order to access the website. Tor Browser is available on Windows, MacOS, Linux, and Android, and can be downloaded here.
How Do I Safely Access The Darknet?
Husain Parvez is a Cybersecurity Researcher and News Writer at vpnMentor, focusing on VPN reviews, detailed how-to guides, and hands-on tutorials. Husain is also a part of the vpnMentor Cybersecurity News bulletin and loves covering the latest events in cyberspace and data privacy. If you’ve gone through this list, you’d agree that each of these can be termed the best deep web search engine in one or the other way.
- Use categorized directories or reputable search engines to reduce the chance of clicking on spam or malicious links.
- Before exploring, make sure you’re familiar with the laws in your jurisdiction.
- Therefore, users should exercise caution and conduct their own due diligence when following search results provided by Grams or any other darknet search engine.
- Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web.
- We set out to build TorDex to be fast and user-friendly, ensuring that it delivers meaningful results without limiting what can be indexed.
- One option is to try DuckDuckGo’s .onion version, which is great for privacy.
DuckDuckGo is a reputable US-based software company, so their Tor site itself is safe to use. That said, you still might get malicious links in your search results, so you still need to proceed with caution with any page DuckDuckGo takes you to. While many dark websites appear sketchy, The New York Times is an exception. It offers reliable news coverage without exposing readers to harmful or illegal material. Unlike the surface web, where pages are easily searchable, dark web sites use encryption to hide their IP (Internet Protocol) addresses.

How To Access The Dark Web Safely

Yes, you can still be tracked on the dark web despite its privacy features. Tracking can happen through IP leaks, browser vulnerabilities, or malicious exit nodes. To reduce this risk, use the Tor Browser properly, keep your software updated, avoid sharing personal information, and pair it with a reliable VPN. Following best practices for online anonymity helps, but staying cautious is essential since no method is completely foolproof.
Free options like NotEvil provide similar breadth without costs but lack premium’s precision tools. Premium is worth it for professionals monitoring trends, while free suffices for beginners exploring basics. Avoid clicking unverified links from results, and cross-check with directories to prevent phishing.
How Can I Verify A onion Site’s Authenticity?

SearXNGSearXNG is a meta-search engine that aggregates results from various sources. Its customizable settings allow you to tailor your search, ensuring a broad yet private overview of available content. Yes, Onion.live and Haystak provide real-time updates and search functionalities for .onion sites. OSINT professionals use the dark web to gather intelligence from hidden forums, marketplaces, and databases that provide early indicators of cyber threats and leaks. It provides easy access to information for researchers, journalists, and many other purposes.
Since the search results come from multiple sources, it becomes incredibly challenging for any entity to control or manipulate the information presented to the users. This decentralized approach ensures that the search results remain unbiased and free from any external influence. To enhance privacy, avoid logging in or divulging identifying information. Additional tools like VPNs or proxy chains can further fortify user privacy.
Browse The Dark Web Securely With A VPN
Riseup is available on the surface web, but its presence on the Tor network extends its privacy benefits by letting you use its services without exposing their real-world identities. You can access encrypted email services through the onion site without getting tracked. Yippy is a search engine that started in 2009, since then it has evolved. To become a leading provider of business learning and knowledge for all types of data users and consumers. This virtual bookstore is one of the oldest search engines on the internet. It was created by “Tim Berners-Lee”, who was also the creator of HTML and the Web itself.
- This isolates any potential malware and prevents cross-contamination with your personal data.
- Furthermore, Grams takes a proactive stance against illegal and harmful content, aiming to filter out such listings from its search results.
- “Hidden Answers” is a community in Darknet, where any user can ask about the use and the investment when buying BITCOIN.
- It’s simply a part of the internet that isn’t indexed by regular search engines and needs special software, like Tor, to access.
- As always, it is crucial to exercise caution and adhere to legal and ethical boundaries when navigating the darknet.
DeepPaste
Risks include data theft via fake sites, legal exposure from accidental access to prohibited material, and deanonymization if JavaScript is enabled. Mitigate by using verified links, real-time antivirus, and pairing with filtered alternatives like DeepSearch for safer, targeted queries. Filtered engines (Ahmia, NotEvil) and directories (Torlinks) minimize dangers, while unfiltered tools (Torch, Haystak) require expertise. Balancing these trade-offs with robust security ensures safe, ethical exploration.



