
Our goal is to empower you with reliable information and resources, making your dark web experience as secure and informed as possible. Even with directories like the Hidden Wiki, users should always be cautious. Never share personal information, avoid clicking suspicious links, and consider using additional layers of privacy like a VPN. The dark web offers privacy and anonymity, but that also attracts malicious actors. The Hidden Wiki is one of the most well-known directories on the dark web, serving as a gateway for users looking to explore .onion sites securely and anonymously.
Major news outlets like The New York Times, The Economist, and The Guardian host SecureDrop instances on the dark web to give sources a safe, anonymous way to share sensitive information. To access them, copy and paste the hyperlinks provided into the Tor browser. The dark web is a part of the internet that isn’t accessible with regular browsers or search engines like Google and Bing. To explore it, you need special tools like the Tor browser (short for The Onion Router) and search engines designed specifically for the dark web. That is why in 2006 they created “the most private search engine in the world”, which does not record, track, or share your personal data.

Is The Hidden Wiki Illegal?
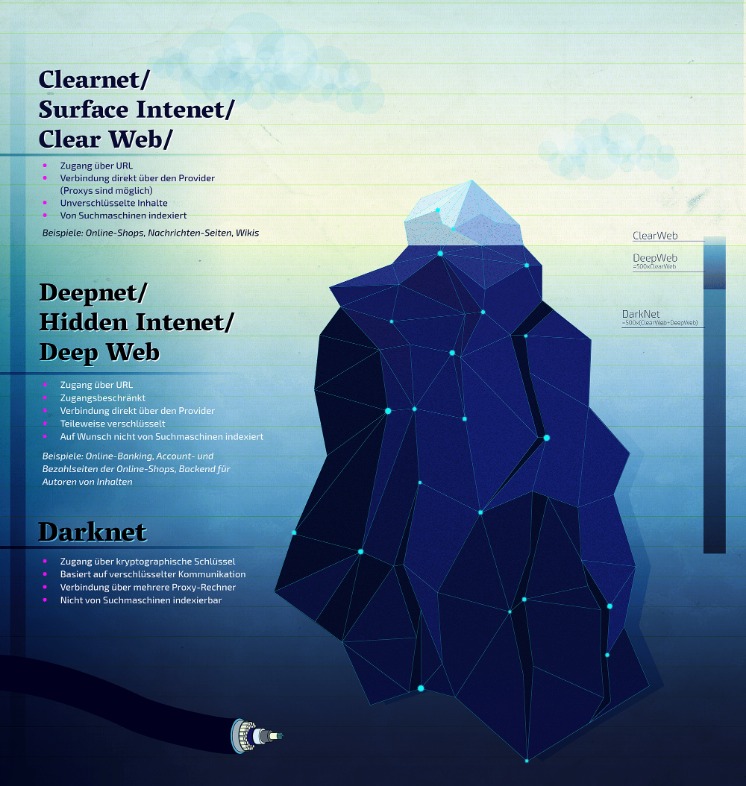
Naturally, this makes the dark web a breeding ground for illegal activity. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. It’s a hidden collective of sites that you could only access through a special browser. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content.
Which Is Better — Tor Over VPN Or VPN Over Tor?
To access the dark web, you will need the Tor browser, which provides the necessary anonymity and security. This is why it’s crucial to always check for updated Ares links from trusted sources before attempting to access the marketplace. That ensures trust and safety for every user exploring Ares darknet products. For security reasons, we don’t display full onion addresses publicly. What distinguishes Ares from other markets is its innovative approach to dispute resolution, multi-signature escrow system, and vendor verification process.
Other Hidden Sites
BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. Exodus Marketplace started to become popular after the shutdown of Genesis Market, and it replaced it successfully. It claims to control more than 7,000 bots from 190+ countries, with data prices ranging from $3 to $10, based on the quality it offers. The marketplace has a simple interface, lets users filter logs easily, and accepts Bitcoin, Monero, and Litecoin for payments.
Report It To The Authorities (if It’s Safe To Do So)
On the dark web, traffic is routed through multiple server nodes that don’t log activity, obscuring the user’s origin and enabling anonymous communication. Staying safe on the dark web requires even more vigilance than the public internet. Scammers and criminals are lurking everywhere to take advantage of the unwary. Follow the pointers below to avoid becoming a victim if accessing the dark web.
Common Mistakes To Avoid
Also, try its services risk-free with the 30-day money-back guarantee. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. Immediately close your entire Tor Browser window (not just that active tab).
Saved Searches
They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. The dark web exists inside layered proxy networks, known as darknets.
- In the end, he was sentenced to life in prison for running one of the largest and most scandalous dark web cases in history.
- Using a virtual private network (VPN) masks your real IP by routing your internet traffic through a secure server, making it appear as though you’re browsing from a different location.
- This virtual bookstore is one of the oldest search engines on the internet.
- It’s somewhere Google and Bing don’t index, and you need special tools to get to it.
- Attempting to reach these sites through regular browsers will result in connection errors.
Darknet Market
You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. Safe browsing on the Hidden Wiki requires a combination of technical precautions and behavioral discipline.
The search engine provides several special features beyond the original word. These include weather forecasts, maps, calculations and Boolean operations as inclusion or alternatives among others. Find working dark web links here, hidden wiki provides access to dark net links and markets. Proton Mail’s dark web version provides end-to-end encrypted email with enhanced privacy protection. The service doesn’t require personal information to create an account and works seamlessly through Tor. I found in my tests that all features work identically to the regular version.
Is It Safe To Visit onion Sites On The Dark Web?
Users must utilize the Tor Browser or similar anonymizing software to access these hidden resources. Navigating the dark web often begins with accessing .onion links—specialized web addresses accessible only through the Tor network, designed to provide enhanced privacy and anonymity online. These hidden sites host a variety of content, from private forums and secure communication channels to whistleblower platforms and marketplaces. In this guide, we’ll explore essential tools and best practices for locating and verifying working .onion links and their mirrors safely and effectively. It acts as a centralized hub to access sites that are not indexed by traditional search engines like Google. Many users rely on the Hidden Wiki to find reliable dark web resources safely and efficiently.

SecureDrop is a really awesome Tor service that can be used to share information without revealing your identity. Many news publications (including many of the ones listed above) use SecureDrop on their .onion sites. The deep web is the part of the internet you can’t access through search engines like Google and Bing. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web. To look at it in a different way, it makes up between 90% and 95% of the internet.
Later, in 2013, Silk Road caught the attention of law enforcement and policymakers like US Senator Charles Schumer, who publicly called for a federal crackdown. That push led to the arrest of Ross Ulbricht, the founder of Silk Road, after a long and intense investigation. Remember, staying informed is your best defense against misinformation. When you know what to expect, you’re less likely to fall for a trick and should be able to keep your identity safe. Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. It’s also a marketplace for digital mercenaries; you’ll find everything from solo hackers offering their skills to well-organized groups that take on more complex or high-stakes projects.
As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing.
Also, you can set a strong password to protect your message and choose how long it will take to expire. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. mark it means it has been verified as a scam service and it should be avoided. The Internet is a vast and complex landscape, much larger than the familiar interface we use every day. We are a passionate team dedicated to bringing you the latest news and insights. Our mission is to provide accurate, reliable, and engaging content that keeps you informed and inspired. Following the closure of Silk Road, various successor markets emerge, but none capture the same level of notoriety or impact.}



