Data breaches often lead to sensitive corporate information appearing on the dark web, which can fuel further attacks. A security gap analysis can help businesses identify vulnerabilities that hackers exploit to compromise their data. Additionally, investing in cybersecurity services for small businesses ensures stronger defenses against threats originating from these illicit platforms.
Cryptocurrency: Fueling Anonymous Transactions
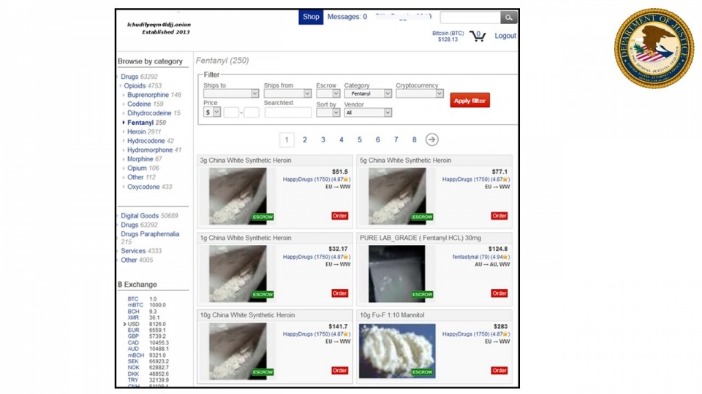
Due to being the most popular and the oldest coin, Bitcoin is traceable. However, Monero, on the other hand, is untraceable and the most trusted payment method on these markets. Therefore, most cybersecurity experts recommend using Monero while shopping on darknet markets. The anonymity and lack of rules that define darknet marketplaces are exactly what make them breeding grounds for fraudulent activities. Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky. Many people go to the dark web to buy things they can’t find elsewhere, but what if what you’re buying is also trying to harm you?
How To Stay Safe From Dark Web Threats
Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services. They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity. BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. The market facilitates trades in stolen credit card data, hacked bank accounts, and services to facilitate the laundering of cryptocurrency.
In light of this, we have chosen the parameters conservatively, obtaining estimates for the number of sellers that are in general smaller than the ones produced by other methods. Second, our approach does not explicitly classify buyers, which are entities that were not classified as sellers. There is a gray zone in which some sellers and buyers may not be easily distinguishable in transaction networks. For instance, there may be sellers that make a small amount of transactions, or spend more than receive, which we would classify as buyers. Future work may further extend the approach presented here, for example using machine learning methods to capture further behavioral regularities. Third, at any given moment we classify entities as either buyers or sellers.
Alright, let’s get into the meat of it—the darknet markets that are ruling 2025. I’ve been poking around these places for a while now, from the giants like Abacus to the old-timers like Vice City. This isn’t just a quick list; it’s the full scoop on what they offer, how they keep things tight, and why they’re worth your time—or not. Whether you’re new to the dark web or a vet who’s seen it all, you’ll find something here to chew on. Below, I’m breaking down each market with everything I’ve picked up—listings, quirks, the works.
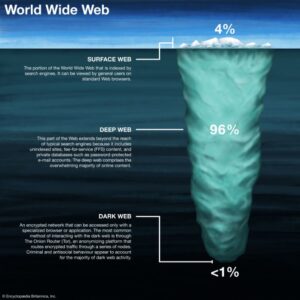
In 2025, the landscape of darknet markets continues to evolve, offering users enhanced security and reliability for drug trade. These platforms leverage advanced encryption technologies and decentralized systems to ensure transactions remain private and secure. The integration of cryptocurrencies like Bitcoin and Monero further strengthens the anonymity of buyers and sellers, making it nearly impossible to trace financial activities. The dark web remains a mysterious yet highly dangerous part of the internet, where illicit activities and black markets thrive. While it offers anonymity for legitimate purposes, it is also a haven for cybercriminals.

This ability of dark web communities to thrive in disruptions reflects how dark web market users have become experts at adapting to risks, managing disruptions and rebuilding quickly. The durability of these markets tells us that if policing responses keep following the same playbook, they will keep getting the same results. And by focusing so heavily on these hidden platforms, authorities are neglecting the growing digital harms in the spaces we all use. Market listings on these platforms often carry the same professional touch you’d expect from legitimate sites complete with product descriptions, seller ratings, and even customer reviews. But these sites are far from typical; they offer illegal items that would be seized immediately on the open web. It’s also super important to train employees to spot phishing attempts and other cyber threats.
Throughout the whole period of observation, the dominant category of buyers is market-U2U buyers followed by market-only buyers, representing on average 52% and 42% of all buyers, respectively. The U2U-only category is comparatively small, representing only 6% of all buyers on average. The number of market-U2U and market-only buyers also drops as a consequence of operation Bayonet. However, compared to sellers, the drop is notably smaller, and the number of buyers rapidly recovers to previous values. Moreover, the number of multibuyers increases, which suggests a fast response from buyers to external shocks by trying to diversify their sources. During 2016 and 2017, AphaBay becomes the dominant market (see Fig. 3), polarizing sellers around its own ecosystem, such that the fraction of multisellers decreases to 10% of all sellers until its closure.
How To Avoid Phishing Scams And Malware Threats
All that one can expect from a deep web marketplace when it comes to anonymity and security. The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. The layers of encryption hide your data and activity from snooping eyes. These markets rely on encryption, escrow systems, and vendor ratings to function in a trustless environment.
Set Up Tor Browser
Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites. On average, the marketplace consists of more than 11,000 items and 1000 vendors. But since its relaunch, the developers are focusing more on operational security and ensuring that users can have a good experience on this site.
The Magical Comeback: Kaspersky And BIZONE Report New PipeMagic Activity In Saudi Arabia And Brazil
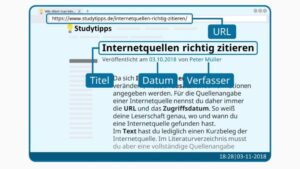
Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers. Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity. Decentralized technologies now underpin a new generation of dark web markets. These platforms run on peer-to-peer protocols without central servers or administrators.
Risks And Dangers
In fact, some of the most profitable illegal digital products on the dark web are crypto accounts, online banking credentials, and e-wallets. Vendors on Hydra also offered services such as “Hacking for Hire,” “Ransomware as a Service” (“RaaS”), and a myriad of money laundering features. Though the drug transactions were limited to Russia and its geographic neighbors, the cyber and money laundering tools were available to anyone in the world willing to pay.
Both works find out that the business models of these markets is maturing. Wang et al. 34 compared Chinese and Occidental dark web markets, covering briefly some aspects of the security mechanisms they employ. During the heights of the COVID-19 pandemic, in 2020, Bracci et al. 6 analysed COVID-19-related products over a period of approximately eleven months.
- The layers of encryption hide your data and activity from snooping eyes.
- These days, it lists over 11,600 illegal items, including hard drugs, hacking tools, and all kinds of cybercrime services.
- If you’ve ever experienced an uptick in phishing attacks and spam after a data leak or breach, it may be because your personal information has been posted to the dark web.
- Our findings suggest that understanding the behavior of key players in dark web marketplaces is critical to effectively disrupting illegal activities.
- Then, we investigate both market star-graphs and user-to-user networks, and highlight the importance of a new class of users, namely ‘multihomers’, who operate on multiple marketplaces concurrently.
At the same time, when using this mechanism, the transaction funds do not need to go through the market’s wallet address. Information is gathered either while running a customised crawler or manually accessing the markets. The next subsection provides an overview of the customised crawler we implemented for conducting this research.

Topics And Products Sold
It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there. You can even find things such as BIN checkers and PayPal cookie converters. Another reason the Russian Market is so popular is that it’s pretty inexpensive compared to other dark web marketplaces.