While exploring the dark web can offer valuable privacy benefits, it’s crucial to understand common risks and how to manage them effectively. By proactively avoiding these common pitfalls, you can significantly enhance your security and safely navigate the complexities of the dark web. Whether you’re curious about the hidden corners of the internet or need practical tips on navigating it, we are here for you. Engaging with the dark web securely requires preparation, awareness, and the right tools. Here are some of the ways to reduce the risks that come with using the dark web.
We have never received a compensation in any form for operating this website. We are not responsible for any harm or loss you may receive by following links listed on this site. Onion sites, and darknets in general, can host some horrifying content. A large amount of it is fictional, but there is no doubt you can end up viewing potentially damaging and compromising material if you are not careful.
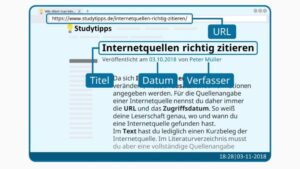
- Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff.
- Crypto services use various measures to keep cryptocurrency wallets secure and make sure your Bitcoin is safe.
- Most people start by using the Tor Browser, which hides your IP address.
- The Tor browser allows you to browse the internet anonymously and visit inaccessible sites.
- Insights like these help researchers and advocates understand how and why Tor is being used.
What Is The Deepest Search Engine?
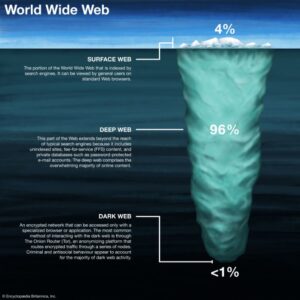
Google only indexes websites on the open web (freely accessible and public), while dark web sites use .onion domains that are not visible to traditional search engines. Unlike other dark web search engines, DuckDuckGo doesn’t index illegal content, focusing instead on providing safe, unbiased results. The surface web, what most users think of as “the internet,” represents only about 10% of total internet content.

BBC News /persian فارسی
You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous.
Verifying The Safety And Reliability Of onion Links

To access them, copy and paste the hyperlinks provided into the Tor browser. The dark web is shrouded in mystery, but not every onion website is dangerous. But before we start, install Norton VPN to help protect your digital identity and stay safer online. While it may have a reputation for seedy and dangerous content, many dark web websites are legitimate and useful resources. Keep reading for a rundown of the best dark links you might want to check out.
Is It Legal To Access Dark Websites?

Browse to the download location, find the Tor Browser folder, and select Start Tor Browser. Qubes is used by journalists, as it is directly used to run SecureDrop, another dark web website on our list. While there are many great Linux distributions to work with, Qubes should be high on your list if you value privacy.

Is DuckDuckGo A True Dark Web Search Engine?
As you continue your online journey, keep expanding your knowledge of digital privacy and security. The more you understand, the better equipped you’ll be to navigate safely and confidently, no matter where your curiosity leads you. To help you make educated choices about cybersecurity to keep you (and your data) safe and secure, by providing detailed, accurate, and practical information based on thorough testing. Watch for unexpected changes in system performance that could indicate malware.
- Some users also share links on encrypted apps like Telegram or Keybase that you can check.
- It’s a popular choice for users worried about online surveillance and data collection.
- At $9.99/month, you can migrate to a premium plan with 500 GB storage and unlimited messages.
- It includes everything you need to go through a login page to access, such as webmail accounts, social media pages with restricted access, online banking sites, web forums, and much more.
This makes your data unreadable in case anyone tries to intercept it. Connecting to a VPN before using Tor to access .onion sites can help keep your sensitive information private and your online activities secure, no matter where you connect from. The extensive database of OSE yields thousands of results for various search queries, ensuring comprehensive coverage. While news and map searches are restricted to the clearnet, OSE offers a diverse array of multimedia search options within the dark web. Unlike conventional search engines, not Evil employs a unique ranking system based on user clicks.
Bobby Search
However, please note this article is for research and educational purposes only. The dark net is full of notorious hackers, scammers, malware, and other viruses. We recommend using NordVPN and a robust antivirus like TotalAV to keep you safe while browsing the dark web. Tor Search constantly crawls (onion) websites 24 hours a day, 7 days a week. In addition, it also revisits already indexed sites to update discover and remove downed and offline sites.
Using Onion Over VPN — All You Need To Know
Here are some things to keep in mind while browsing your favorite dark web websites. The anonymous group behind Tunnels alleged that the materials were produced while exploring the forbidden tunnels, built underneath some of the most prestigious American Universities. No info is available on the explored institutions or how these sections can be accessed.

Safety Tips For Using The Dark Web
Just like Facebook, this is no random namesake; it is a legitimate platform from which to reach the CIA anonymously. You can even apply for jobs and request information, among other things. People like spies or whistleblowers often contact the CIA via the dark web to keep themselves hidden.
How Does The Tor Browser Work?
While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network.