With less than two years of existence and the widest assortment of listings for both physical and digital goods, Tor2Door is one of the largest darknet markets as of 2022. It has a unique design, and according to its administrators, it built the market from the ground up. This undoubtedly gives Tor2Door a distinctive feel, yet it is also simple to use.
Content includes non-indexed websites, apps, and resources, which can include protected information such as, online banking, specialized databases, non-linked and password-protected websites, and more. It includes media and archives which cannot be crawled and indexed with current search engine technology. You can tell you’re on the dark web if you’re accessing websites with .onion addresses on the Tor Browser or a similar anonymity network.
Using DuckDuckGo over Tor will also let you see onion sites and normal pages in your search results. While many dark websites appear sketchy, The New York Times is an exception. It offers reliable news coverage without exposing readers to harmful or illegal material. Technology can bridge this gap and supplement threat intelligence with the context necessary to understand threat actors and anticipate future attacks. Now, thanks to more context and more threat intelligence, it’s a place where defenders can gain the edge. However, it’s always a good idea to exercise caution while engaging with darknet markets.
The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web.
Découvrez Notre Liste De Sites Darkweb Fiables
French authorities have dismantled their third dark web marketplace over the last four years after they seized control of “Le Monde Parallèle” (The Parallel World) last week. If you are already a registered user of The Hindu and logged in, you may continue to engage with our articles. If you do not have an account please register and login to post comments. Users can access their older comments by logging into their accounts on Vuukle. For several years, Yahoo was at the apex as the internet’s best web service provider, offering…
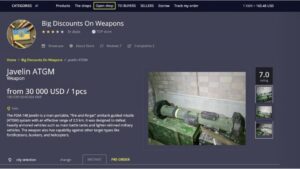
One of its main features is a huge quantity of illegal marketplaces selling drugs, weapons, stolen bank cards, fake IDs and more. But hidden among the criminals and buyers are French units of specialised police forces, who are hunting down cybercriminals. The Dark Web is too often mistaken for the « Deep Web », or « invisible web », which refers to content which is not indexed by general search engines such as Google, Yahoo or Qwant.
Can You Be Traced On Tor?
ZeroBin offers an extra secure version of this service by only encrypting and decrypting text in the browser, meaning their servers have no knowledge of what is passing through it. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts. Archive.today is considered an important tool to track changes across government and corporate websites, preserve cultural heritage, and keep knowledge outside of autocrats’ reach. You can archive any site you want, or retrieve historical records wherever available. Simply accessing the dark web and using the Tor browser may already raise government suspicion.
Cybersecurity Grand Prix: VPNs And A 1-2 Race Finish
It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor.
Alleged Collection Of 1 Million Israeli Card Holders Data Offered For Sale

Following the NYT, the BBC launched a dark web “mirror” of their international edition in 2019. Note that some features of the normal website are not available on the .onion version, including BBC iPlayer. Agents from the DNRED intelligence agency seized nearly €4,000 (US$4,640) in cash and around €25,000 in online currencies while swooping on the suspects in four simultaneous raids around France.

How To Use Tor, And Is It Safe To Access The Dark Web?

In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions.
Social Media
Accidental leaks at the Tor entry nodes can potentially expose your IP address. On top of that, the provider offers perfect forward secrecy (PFS). A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. It is imperative to stay alert and trust your gut when on the web. Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee.
- 26% of users in North America and 17% of users in the EU access the Dark Web daily, with 3.29% of those users coming from France.
- The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines.
- Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations.
- However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it.
- It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products.
You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. The process costs a fee, but unlike other “tumbler” or “mixing” services, there is no risk that Wasabi or any of its users could scam you out of your coins. One of the most popular ways to get around the dark web is not to use a search engine at all.
Pourquoi Devrais-je Utiliser Un VPN En Naviguant Sur Le Dark Web ?
- From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains.
- While many dark marketplaces have been shut down by authorities, new ones soon appear in their place.
- On top of that, the installation process of Freenet is rather easy.
- However, there are some significant variances in the background despite the similarities.
- As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web.
Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
No, it isn’t illegal to browse the dark web, and there’s nothing inherently wrong with visiting a Tor website. Info like your name or email address never needs to be shared on the dark web. You should also limit the number of financial transactions you make on Tor banking portals.