And I liked that if I visited a site that had a .onion version, it prompted me to switch to that version. Some banks and other financial institutions only require two pieces of identification to open a new account. With a stolen passport and driver’s license, for example, fraudsters can open accounts and collect the signup rewards in the victim’s name, or use the account as a mule to cash out on other illegal transactions.
About Amicus International ConsultingAmicus International Consulting assists individuals in legally obtaining second citizenship, establishing privacy, and relocating securely. From identity resets to global compliance consulting, Amicus is a trusted partner in complex cross-border transitions. The dark web may sell a kind of freedom, but it is a fragile and dangerous one. With every tightening of global surveillance, biometric border control, and real-time customs databases, those using forged or stolen identities risk immediate detection, imprisonment, and irreversible bans. Rather than rely on dark web routes, the client worked with Amicus to obtain a second passport legally through a Caribbean nation’s CBI program.
III Production And Distribution Channels Of Fake IDs
ZLibrary hosts free file-sharing access to academic texts, scholarly articles, and general-interest books. It often hosts copyrighted materials without permission, violating many countries’ copyright laws. Downloading or distributing such material is against the law and can have legal consequences. Our customization process ensures your ID doesn’t just look real—it fits your story. With us, you get an ID that’s tailored to you, down to the smallest detail.
How To Find New, Active Dark Web Links
- Given the anonymity and encryption inherent to the dark web, authorities have adapted by developing specialized investigative methods and cross-border cooperation.
- Users’ identities are safe from the prying eyes of governments and corporations.
- As with our previous reports, we gather data by scanning Dark Web marketplaces, forums, and websites.
- By investing in education, job training, and community outreach programs, society can reduce the demand for counterfeit documents and create safer, more inclusive communities.
- You can also run a dark web scan to see if your information has been leaked on the dark web.
The “surface web,” on the other hand, is the publicly available part of the internet that search engines index. Card data is a hot commodity on the dark web, with credit card details and cloned cards being sold to cybercriminals. These stolen cards can be used for financial gain through unauthorized charges, account takeover, and identity theft.
Dark Web Vs Deep Web: What’s The Difference?

We quickly ran the ID through our software to see if the barcode generated by CloudPassport would fool any of our barcode security tools. The AI-generated fake ID does not pass our identity verification software. As members of the World Wide Web Consortium (W3C), we uphold the standards for the World Wide Web and work towards a more secure and user-friendly online experience. Identity.com is an open-source ecosystem providing access to on-chain and secure identity verification.
How Much Does It Cost For A Scammer To Hack Your Email? The Answer Is Probably Less Than You Think
Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. That alone might already raise suspicion and place you under special surveillance. Some reports say the FBI will simply label you a “criminal” once they’re aware you’re using the Tor browser. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post.
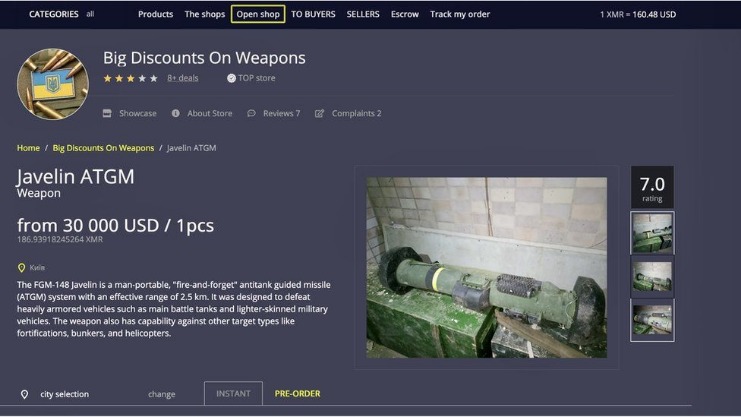
Although paying with fiat currencies like the US dollar is an option, many of these dark web-based services require payment made with the flagship cryptocurrency, Bitcoin (BTC). This cryptocurrency was initially used on the dark web as an untraceable payment method to purchase goods or services. While many authorities now have the power to trace BTC transactions, Bitcoin is still the preferred method of payment on many dark web marketplaces. Additionally, communities facing rampant document fraud often see declining public trust in institutions, businesses, and even interpersonal relationships. When citizens perceive that fraud is widespread or tolerated, social cohesion weakens, damaging overall community resilience and stability.
Explore Our Range Of Realistic Fake IDs
Offers a long history of operation, with a reputation for delivering high-quality products. Biometric technology is leading the charge in next-generation verification. Tools like face match and liveness detection are no longer futuristic concepts; they’re becoming the gold standard for security.

Abacus Market
Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. To expand their reach, some marketplaces established parallel channels on Telegram. This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. State-issued IDs are sealed with professional-grade laminate, a material not available to the public.

Innovations In Anti-Counterfeiting Technology

In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. In 2023, the dark web attracted an average of 2.7 million daily users, with Germany now leading as the country with the highest number of Tor users, surpassing the United States for the first time in years. Suppliers that specialize in fraud detection have the equipment and software to scan, analyze, and evaluate IDs, ensuring that they are authentic. Anyone who has the desire to purchase a counterfeit ID is able to access any number of websites that will be delighted to do business with them.
Solutions To Combat AI-Generated Fake IDs
It offers features like encrypted communication for chats and file sharing, making it popular with privacy-conscious individuals. Sci-Hub provides free access to scientific papers, with millions of documents. Scientific journals often put their articles behind a paywall and charge high fees for access, but Sci-Hub offers open access to read or download research papers. While it’s a deep resource, it’s also illegal in many countries, because it may violate copyright restrictions, so check out the laws in your area before visiting.
Long-Term Impact Of Fake Document Use
What’s even more alarming is that fake ID usage isn’t limited to this younger demographic. This fake ID report also points out a growing trend among adults who use fake IDs for fraud and financial crimes. This shift highlights how these counterfeit documents are no longer just tools for underage drinking but are now playing a role in more complex criminal activities. Since then, BidenCash has continued to operate using the “dumping” method.
Leaked credit cards from Telegram channels account for the overwhelming majority of compromised payment card details. Card Shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information. Some threat actors offer a “complete package” known as “Fullz”, which includes full personal details and financial information like bank account details or social security numbers. While fake IDs may seem like a harmless way to sneak into bars, the risks are real. Students caught using them can face fines, criminal charges, and even expulsion. In Texas, for instance, possession of a fake ID is a Class C misdemeanor, punishable by up to 180 days in jail and a $2,000 fine (Doug Murphy Law Firm, 2024).