It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. With the onion browser, you can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. It works by sending internet traffic through volunteer-operated nodes all over the world.
Did The Silk Road Marketplace Go Under?
Finally, product variety significantly influences marketplace choice. Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users. An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions.
A Cross Between Monokai And One Dark Theme Press Ctl/command + Shift + P To Launch The Command Palette Then Run Ext…
What’s dope is their forums—real talk, not just noise—building trust like Telegram’s side hustle vibe. Escrow’s standard, keeps things fair, and I’ve never seen it glitch out. For 2025, they’re hyping a peer-to-peer escrow twist—could cut out middlemen and shake up how deals flow, which I’m stoked to see play out.
The Escrow Process

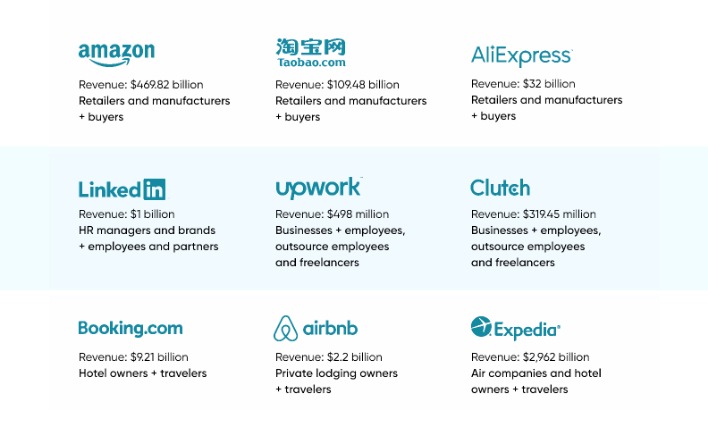
However, the goods and services offered include stolen credentials, hacking tools, counterfeit documents, drugs, and weapons. Escrow services are commonly used to hold funds until transactions are completed, ensuring a level of trust between buyers and sellers despite the illegal nature of their dealings. Dark web marketplaces are like the hidden corners of the internet where illegal activities take place and even thrive. These markets operate on the dark web, a part of the internet that’s not indexed by traditional search engines and requires special software, like Tor, to access. Here, you can find anything from stolen credit card information and personal data to illicit drugs and counterfeit goods. AlphaBay marketplace is one of the oldest dark web marketplaces.
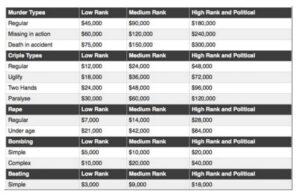
Illegal Substances And Weapons
However, legal bodies and law enforcement operations made this impossible and shut down these illegal communities. Genesis Market and BidenCash, two top dark web marketplaces, were also shut down in 2023 and 2025, respectively. From there, these products are then passed on to distributors, which are the dark web marketplaces in this context. On these marketplaces, they’re listed, sold, and promoted just like items on any e-commerce site. This can include everything from full names, email logins, and passwords to credit card details, social security numbers, and bank account information. The cybercriminals trade even sensitive documents, such as medical records, passport information, and driver’s licenses.
Tips To Stay Safe When Using The Dark Web
Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services. They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity. The site allows users to find and buy a vast variety of products and services.
The dark web poses significant risks to small and medium-sized enterprises (SMEs), which are often ill-equipped to handle the sophisticated threats emerging from these hidden networks. Compromised credentials, stolen intellectual property, and leaked sensitive data regularly surface on dark web marketplaces, exposing SMEs to severe financial and operational consequences. Dark web marketplaces are structured platforms that mirror legitimate e-commerce websites but thrive on anonymity and untraceable transactions, often conducted through cryptocurrencies. According to a report by Kaspersky, a single stolen credit card can be purchased for as little as $15, while entire company databases are sold for significantly higher sums. These transactions present an ever-growing threat to businesses, particularly small and medium-sized enterprises (SMEs), which often lack the resources to counter these risks effectively.
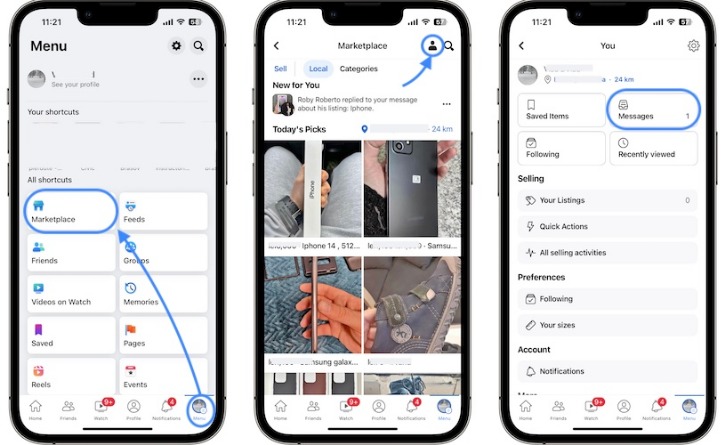
Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. There are a lot of misconceptions about the dark web online and in popular media. When most people refer to the dark web, they are thinking about dark web/darknet marketplaces (DNMs). A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops.
Making Cybercrime Easy For Anyone

Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user.
- Customers may lose trust in an organization’s ability to safeguard their data, resulting in client attrition and long-term harm to the business’s brand.
- This can include everything from full names, email logins, and passwords to credit card details, social security numbers, and bank account information.
- Immediately close your entire Tor Browser window (not just that active tab).
- Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal.
- Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats.
- The dark web poses significant risks to small and medium-sized enterprises (SMEs), which are often ill-equipped to handle the sophisticated threats emerging from these hidden networks.
It’s recommended not to use new alternative links as they could just be planned exit scams. The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. As stated above there are other areas and goods that are sold on this market. There are currently 50 listings in this section, second only to gadgets, which sells products such as phones and computers. A range of different drugs are made available and a varying range of prices.
Shades Of Purple Theme For VS Code
Every time the vendor responds saying “Yes worldwide” or “Yes without problems.” It is unclear what shipping methods this vendor is using. Although some other vendors state that they use FedEx and FedEx international to ship overseas. Reviews are what most DNMs rely on to ensure that they are receiving the products that they are buying. A lot of the time the products for sale sound too good to be true. But as demonstrated below vendors will try to explain why they have received bad reviews.
Implement security features like code obfuscation, app sandboxing, and monitoring for unusual behavior to protect your mobile applications and their users from RATs like DarkShades. You should never use your personal information on the dark web anywhere else in your life. In fact, create new throwaway accounts and documents if possible. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Avoid using payment methods that can easily expose your identity. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people.