
In today’s ever-evolving cybersecurity landscape, patch management isn’t just maintenance �… Regular browsers access much of the deep web, especially sites behind logins. For this guide, we’ll use the Tor Browser as an example, but any other web browser (like Brave) that supports the Tor protocol will work just as well. Other examples of compatible web browsers include the Onion browser, Firefox and Chrome, but the latter two require you to install a separate plugin. The most common way to access the dark web or deep web is by using the Tor network, and doing so is not nearly as complicated as you might think.
¿Por Qué Usar Forest VPN?
Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information.

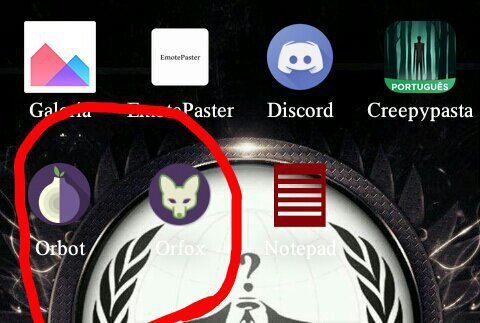
Step 2: Install Privacy-Focused Browsers
However, you might have found yourself asking, What is the deep web? As news outlets rarely concern themselves with explaining exactly what it is besides being a place where you can anonymously acquire illegal goods. All our content is written fully by humans; we do not publish AI writing. Ever tried to access a drive only to be blocked by encryption you didn’t set up—or forgot the ke… Ever wondered, what is cyber security and why it keeps making headlines? Avoid phishing links, unknown files, and suspicious login portals to prevent security risks.
Como Usar Uma VPN Para Acessar A Dark Web
Over 96% of the internet lies beneath the surface web, hidden from regular search engines like Google or Bing. For IT managers, cybersecurity experts, and tech enthusiasts, understanding the deep web is essential—not just for curiosity but for data access, research, and privacy. The deep web — also known as the deep net — is a collective term for non-indexed websites that are invisible to traditional search engines. Because of this, tracking down the web addresses of deep web sites is a much more manual process. Aleksandar Kochovski is a cybersecurity writer and editor at Cloudwards, with a rich background in writing, editing and YouTube content creation, focused on making complex online safety topics accessible to all. With a Master’s in Architecture and experience as an assistant professor of architectural planning and interior design, Aleksandar applies his research prowess to guide readers through the intricacies of VPNs and secure cloud services.
Consejos Para Mantener La Seguridad En Tor:
First, you need a web browser that’s capable of utilizing the Tor protocol. We also have a dedicated guide to the best VPN for the dark web. The dark web refers to the subsection of the deep web that provides illegal services. This runs the gamut from illegal substances to personal information, credit card details, child sexual abuse material and, allegedly, assassination contracts. If you’ve followed the news in the last two decades, you’ve probably heard stories and seen headlines about the deep web or dark web.
Https://g7ejphhubv5idbbu3hb3wawrs5adw7tkx7yjabnf65xtzztgg4hcsqqdonion/
With how mythologized the deep web and dark web have become, you’d be excused for thinking it’s difficult or dangerous to access. In reality, there’s nothing inherently dangerous about accessing either, and doing so is surprisingly simple. Keep reading this guide to learn more about what these terms actually mean, and how you can find your way into the underbelly of the internet. Tor routes your traffic through three random nodes in different countries. Even if someone intercepts the data, they’ll only see an encrypted stream between nodes – not your real IP. Unlike VPNs, Tor node operators don’t keep logs – this has been proven in court, including a major U.S. case against a hosting provider in 2022.
This includes everything from academic databases to medical records, government resources, and confidential corporate documents stored behind login credentials. Although the deep web and the dark web may seem intimidating and dangerous, they’re actually surprisingly simple services to get started with and use. Many use the technology to engage in illicit activities, but there are many legitimate reasons for accessing the deep net, especially in countries with poor digital privacy laws such as the United States. Broadly, this is the process of storing and categorizing the web pages and sites found by the search provider’s crawler bots, so that it can more easily find relevant results when users search for something. Now you know how to enter deep web safely, the key differences between deep web vs dark web, and which best deep web browsers to use.
¿Por Qué Existe La Deep Web?
Tor Browser prevents someone watching your connection from knowing what websites you visit. All anyone monitoring your browsing habits can see is that you’re using Tor. The reason why the deep net provides this level of privacy for website hosts is that the .onion address that you use to access the website obfuscates the actual IP address of the server. This makes it impossible to track down the physical server under ordinary circumstances.
Secure Your Connection

Rule number one – never download Tor from third-party websites. In 2023, attackers distributed fake Tor Browsers with trojans through phishing pages. After installation, verify the file’s authenticity using PGP – the instructions are on Tor’s website.
You could certainly go much deeper into the topic, but we hope the information provided here has given you a basic understanding of what the deep web/dark web are, how they function and why they exist. More importantly, you should now know how to access these hidden sectors of the internet at your leisure. You should consider using data breach monitoring tools to regularly check if your personal information has been leaked onto the dark web.
Trusted Sources To Get Started:
However, since your traffic is routed through nodes that you don’t have any control over, you are at the mercy of whoever operates these nodes. As long as there’s a demand for the ability to privately browse the internet and, more importantly, host websites anonymously, the deep web will exist. Due to its decentralized structure, there is no real way to “shut down” the deep net, just like you can’t really shut down the regular internet. You can also use security tools with AI-powered scam detection capabilities to identify and block suspicious links and websites in real-time when browsing the dark web.
- If you’re going to use the I2P or Tor network to access the deep web — or the surface web for that matter — make sure to install one of the best VPNs to protect yourself against malicious exit and entry nodes.
- Aleksander Hougen, the co-chief editor at Cloudwards, is a seasoned expert in cloud storage, digital security and VPNs, with an educational background in software engineering.
- The network is comprised of thousands of volunteer-run servers known as Tor relays.
- If you’re new to PGP, spend 20 minutes learning it – it could save you from malware.
This is when it takes a search query from the user, finds the most relevant results in the index, and then serves the resulting web pages back to the user. The deep web fulfills a range of needs, from allowing people to host and access digital content away from the prying eyes of authoritarian governments, to facilitating a range of illegal activities. We believe everyone should be able to explore the internet with privacy.We are the Tor Project, a 501(c)(3) US nonprofit.We advance human rights and defend your privacy online through free software and open networks. You can’t use Google to access the Deep Web—you’ll need to go directly to websites and archives to find non-indexed files, or try a Deep Web search engine. Unlike the Dark Web, which requires a special web browser called Tor, you can use any browser to get to the Deep Web.
If you’re new to PGP, spend 20 minutes learning it – it could save you from malware. To advance human rights and freedoms by creating and deploying free and open source anonymity and privacy technologies, supporting their unrestricted availability and use, and furthering their scientific and popular understanding. We always recommend using a reliable VPN when accessing the deep web or dark web. That means that if your incoming traffic is routed through a node operated by cybercriminals, they can inject malware into the code of the response, without you ever knowing that it’s happened. If you use the widest definition of the deep web, then it’s a vast ocean of websites. Most of these are databases and intranet sites that typically aren’t what you’d think of when you hear the term “deep web,” but even if you exclude these, the websites on the deep web vastly outnumber those on the regular surface web.
In this detailed guide, we’ll cover how to access deep web safely, the differences between deep web vs dark web, recommend the best deep web browsers, and explain safety best practices. The Deep Web refers to web data you can’t find using a search engine like Google. Unlike the Dark Web, the hidden corner of the internet often used to conduct illicit or anonymous activity, anyone can get to the Deep Web safely using a regular browser. We’ll show you how to find information on the Deep Web and safely dip your toes into the Dark Web.



