Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Whether you’re sticking to the Surface Web or venturing into the hidden corners of the internet, adopting strong security practices is essential. Below are strategies and tools you can use to safeguard your privacy, minimize risks, and protect your personal data in an increasingly complex digital world. Accessing Deep Web content typically involves straightforward login procedures rather than specialized software. There are possible chances that you all must have heard of the Deep web, Dark web, and Darknet, and sometimes people get confused while differentiating between them.
The Connection Between Dark Web And Cybercrime
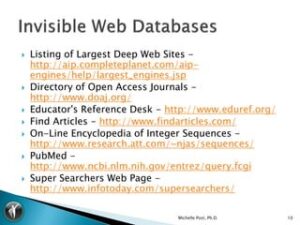
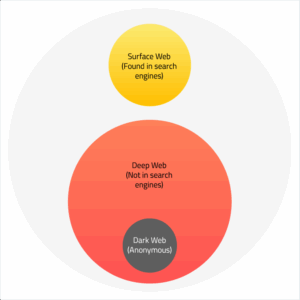
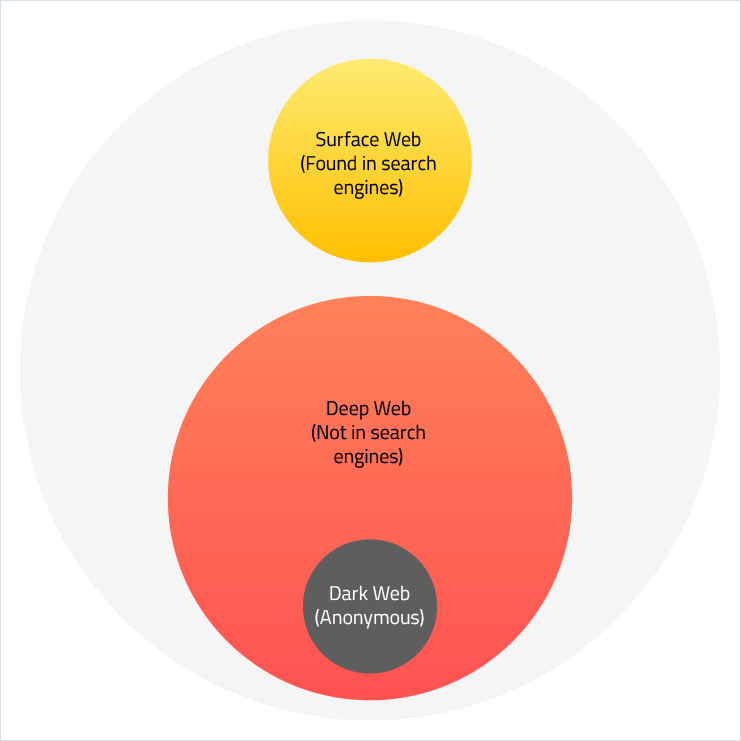
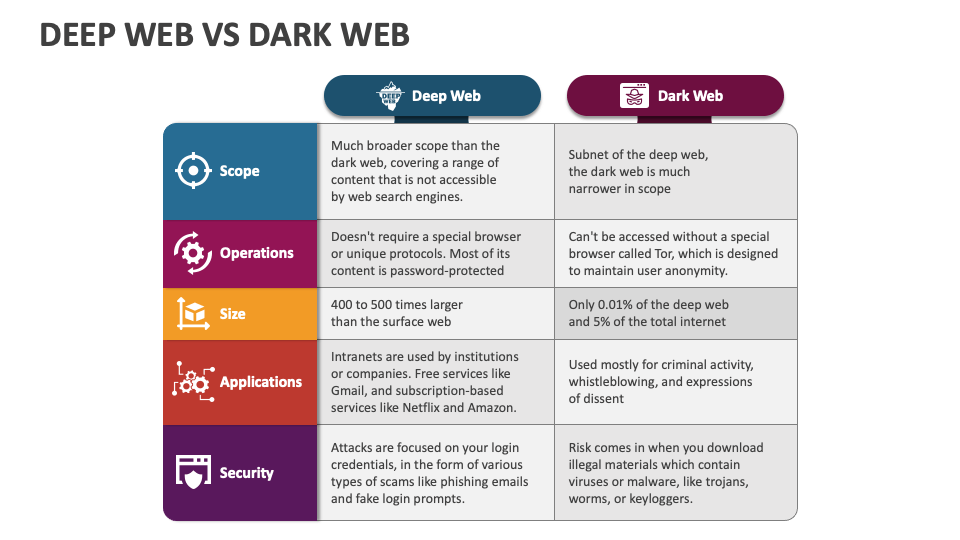
Of course, we know this isn’t true, and the surface web only comprises just a small percentage of the entire internet. Most of the internet is divided up into restricted pockets known as the deep web. Specialized tools exist for deep web searching within specific contexts, but comprehensive indexing remains technologically unfeasible. Understanding the distinctions between the dark web and the deep web environments is essential for developing effective cybersecurity strategies. The dark web deep web difference is primarily in their accessibility methods and intended purposes.
Security Threats
Authentication refers to a requirement of credentials establishing one’s identity in order to access the systems and information. Whether or not the resources are indexed on a search engine, a visitor must possess valid credentials, such as a username and password, to go “deeper” into the site than the login wall. The vast portion of the internet not indexed by search engines, including private databases and password-protected sites, which are primarily used for legitimate, secure data storage. The Internet is an enormous and complicated information network; the overwhelming majority of that is simply not available to any average user. The part that we are most familiar with is really just what we might think of as the surface web.

Accessing the Deep Web generally involves fewer risks compared to the Dark Web, but there are still some considerations. It’s important to note that the Dark Web is not inherently illegal. As a subset of the Deep Web, the Dark Web represents an even smaller, more specialized portion of the online landscape. The Deep Web is estimated to make up a staggering 90% to 95% of the internet, dwarfing the surface web most people are familiar with. However, they refer to different parts of the internet with distinct characteristics and purposes.
Now let’s understand the basics of the Indexed web for better clarity. There’s also a risk of being monitored by state actors or cybercriminals who leverage de-anonymization techniques to identify users. This exposure can lead to legal repercussions if law enforcement tracks illegal activities back to you, despite the anonymity. Understanding the difference can help you avoid potential risks and stay secure online. If the dark web lets users anonymously engage in illegal or dangerous activity, why does the government allow it to stay up and running? There isn’t any one way to access the deep web — it just depends on what you’re looking for.

Transport Layer
However, the dark web is notorious for hosting illegal activities, such as drug trafficking, weapons sales, counterfeit money, and various forms of illegal pornography. On the other hand, the deep web refers to the vast portion of the internet that is not indexed by search engines. This includes confidential databases, academic journals, private social media content, and other information that is not easily accessible to the public. The deep web, also known as the hidden web, is the part of the internet where almost all online activity happens.
Get The Latest Cybersecurity News And Updates Sent Straight To Your Inbox
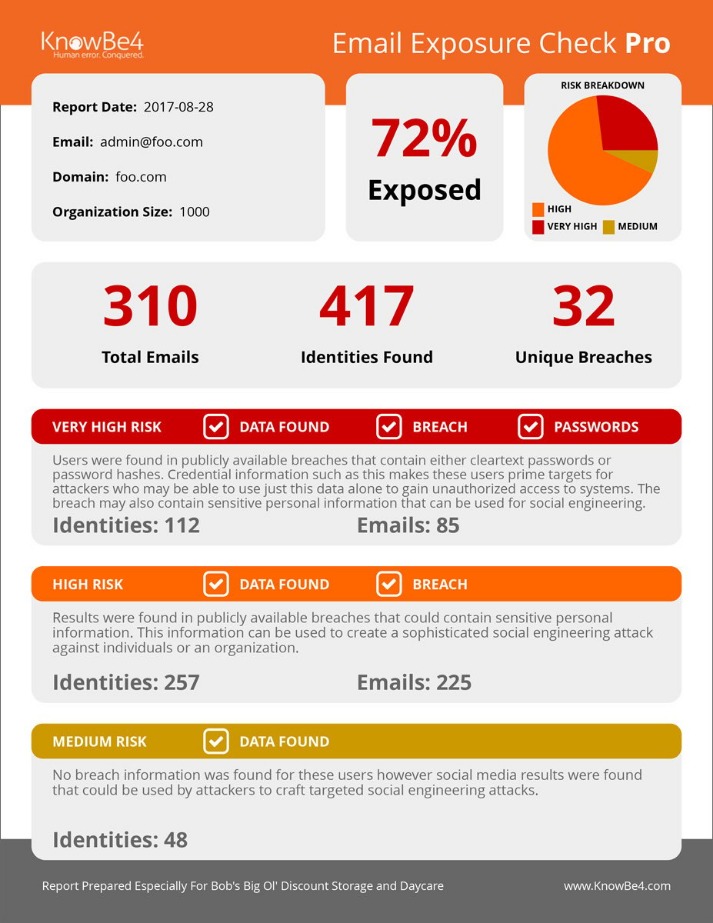
Fortunately, monitoring solutions work around this problem, giving security analysts advanced warning of dark web discussions and potential threats. The next cybersecurity threat to your critical systems and data could be incubating on the dark web as you read this. Without visibility and dark web intelligence, security teams can only wait and hope their network defenses are sufficiently robust. This situation challenges risk analysts and security teams to discover leaked credentials and gather threat intelligence. Companies need to update their threat prevention techniques to monitor dark web environments. However, using the deep web for legitimate reasons is uncontroversial.
- While both are often misunderstood, they serve different purposes and come with distinct risks.
- The deep web is a layer of the internet that’s not indexed by search engines and requires further permissions to access, like a paywalled academic resource or an employee-only corporate website.
- Some people use the Dark Web for legitimate reasons, but prefer to remain anonymous.
- Dark Web users also use the platform to exchange tips and tools for performing different cyberattacks and fraudulent activities.
- It mainly hosts hidden websites that can’t be found on search engines and typical browsers can’t open.
Some examples of legal uses include secure communication for people living in oppressive regimes, communicating with journalists privately, and conducting sensitive discussions on private forums. Think password-protected websites, subscription services, banking portals, and even the private contents of your email inbox. The Dark Web is a small part of the Deep Web, accessible only through specialized tools like Tor (The Onion Router).
How The Dark Web Impacts Cybersecurity
It’s a technology—specifically, an anonymized part of the internet—that anyone can use. It’s a place where activists fighting for freedom and criminals exploiting vulnerabilities can coexist—sometimes on the same platform. What you find depends heavily on where and what you’re looking for. Likewise, whistleblower platforms like SecureDrop are designed specifically for the safe and anonymous submission of sensitive documents to investigative journalists.
Legal Implications
Many VPNs are sluggish, so they will not be suitable for data-intensive tasks. In addition, studies have revealed that many VPNs lack reliable security. The dark web’s infrastructure serves those needing privacy, including activists, whistleblowers, political dissidents, and even regular citizens attempting to escape censorship or persecution. Many mistakenly believe the Deep Web and Dark Web are synonymous but they are distinctly different. Like the Surface Web and even the Gray Web, the Deep Web does not require a special browser like the Dark Web.
Surfing the dark web could cause you to access dangerous websites or illegal content. However, while the internet includes a lot of data we don’t usually see (deep web), the dark web has a reputation for concealing and facilitating criminal activities. One of the most significant barriers to finding deep and dark web sources is that you must use the exact URL to access sources that are not indexed — even with a browser like Tor.
These operating systems send every outgoing request, not just the web browsing ones, through the Tor protocol, ensuring robust protection. Besides, some additional protective measures may include application sandboxing, erase-on-shutdown, etc., based on a particular OS. People use it to share information when their local governments act hostile or snoop extensively. For instance, Edward Snowden used the dark web to reveal that NSA surveils all US citizens, even if someone has no criminal history.
What’s The Difference Between Deep Web And Dark Web?
It has become infamous for providing illegal content like drugs, stolen data, and credentials, among other illicit items. Subscription-based applications can be accessed only once the user has paid for them. The paywall prevents search engine crawlers from accessing this content. Examples include software as a service (SaaS) solutions, paid news websites, and streaming services. These illicit items can sell for anywhere from a few bucks to thousands of dollars.
It includes everything from private databases and academic research to your personal email inbox or corporate intranet. The surface web includes all content indexed by search engines like Google. It’s the part of the internet most people use daily, including news sites, blogs, online stores, and social media.