Some reports say the FBI will simply label you a “criminal” once they’re aware you’re using the Tor browser. Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post.

How To Secure Yourselves Before Accessing The Deep/Dark Web?
And since we can’t access every dark web onion site to see if our own credentials are up for sale, we have some monitoring tools embedded within NordVPN and 1Password. Now you know how to enter deep web safely, the key differences between deep web vs dark web, and which best deep web browsers to use. Whether for professional or personal use, accessing the deep web responsibly ensures privacy, security, and efficiency. The Deep Web aka Invisible Web is simply locations in the Internet where search engines can’t index. However, most are outdated and have not kept up with the changing landscape. For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question.
All of those challenges, and a whole lot of others, make data much harder for search engines to find and index. Keep reading to see more about what separates the surface and deep Web. This index or map is your key to finding specific data that’s relevant to your needs.
Table Of Contents
- The emergence of search engines like DuckDuckGo has also made it possible to search on Tor as you would typically do on Chrome, Edge, and Firefox.
- Before we unpack the dark web’s threats, let’s explore how and why users access these sites.
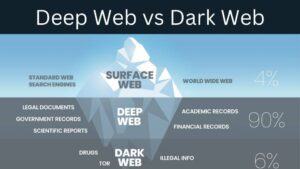
- The internet is made up of different types of content, some of which can be accessed by search engine crawlers and some of which can not.
- However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail.
- It consists of private, secure, often password-protected, content requiring credentials or special access.
Private communications, sensitive corporate data, personal accounts, government records—these things must be protected for reasons of privacy, legality, and security. Just as most of our physical lives take place behind closed doors, so too does the majority of digital life. It consists of private, secure, often password-protected, content requiring credentials or special access. Most activities on the deep web are legal and intended to protect user privacy.
Are Sites On The Dark Web Illegal To Use And Visit?

Neither ZDNET nor the author are compensated for these independent reviews. Indeed, we follow strict guidelines that ensure our editorial content is never influenced by advertisers. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous.
- Government developed Tor so their operatives could remain untraceable.
- A VPN and Tor should be used together and it is advisable to connect via a VPN to Tor, rather than vice versa, for the best protection possible.
- However, these features can be used for both legitimate and malicious purposes.
- Its reliance on volunteer-operated nodes means that some exit nodes may be compromised, potentially exposing unencrypted traffic.
- Beyond his prolific writing commitment, Aleksander helps with managing the website, keeping it running smoothly at all times.
How To Access The Deep Web Using Tor
With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. Even if you’re using a private, anonymized crypto wallet, there are other ways your identity can be revealed—even if it’s something as simple as letting a personal detail slip in an instant message. With deeper visibility, businesses can detect warning signs, monitor for brand-related risks, and react promptly. Whether they are dealing with insider threats or exposed credentials, security teams that understand what happens in the Deep Web gain the ability to respond proactively.
How Does Deep Web Work?
Ultimately, the responsibility lies with individuals to govern their online conduct wisely. Prioritizing internet safety—utilizing encryption, employing secure passwords, practicing cautious engagement—can significantly reduce experiences of danger in both the deep and dark webs. As digital landscapes continue to evolve, so too must our commitment to understanding and navigating these complexities safely. In an increasingly digital world, the internet has become an essential element of our daily lives.
That means that if your incoming traffic is routed through a node operated by cybercriminals, they can inject malware into the code of the response, without you ever knowing that it’s happened. The reason why the deep net provides this level of privacy for website hosts is that the .onion address that you use to access the website obfuscates the actual IP address of the server. This makes it impossible to track down the physical server under ordinary circumstances.
What Is The Deep Web? The Definitive Guide

The simplest definition for the deep web I can come up with is “It is any and all content which is unindexed, and can’t be found via traditional search engines like Google, Yahoo, Bing etc”. It is a part of the WWW that is different from the so-called “surface web,” which is the visible part of the web. For example, reading about illegal activities on the dark web isn’t unlawful. Many whistleblowers and activists use it as a channel to raise their voices and fight injustice without exposing their identity and thus compromising their safety. Basic online hygiene can prevent security lapses when accessing the deep web. For instance, using an unprotected public network to pay your bills might lead to cybercriminals being able to capture your payment information.
Sharing personal information on a deep website or forum can be a costly mistake. Legitimate uses of the Deep Web include accessing medical records, conducting financial transactions, researching academic databases, and managing secure corporate intranets. Organizations must monitor the Deep Web for potential data breaches or unauthorized access to proprietary information. Cybersecurity tools and techniques, such as Deep Web monitoring, help mitigate these risks.
Other Ways To Access Dark Web Platforms
Law enforcement agencies don’t pay much attention to the Gray Web, so users don’t feel the need to be anonymous. Deep Web sites include private databases, restricted content, and other sources of in-depth information about companies and their operations. This makes these sites valuable sources of information if the content is accessible. However, the access restrictions on the Deep Web can make this information more complex and difficult to access.
The average monthly traffic received by the deep web is 50% more than surface websites. The volume of public data on the deep web is 400 to 500 times greater than that of the surface web. The anonymity offered by Tor allows both hosts and users to cloak their identities. By setting up the server correctly, hosts can even mask the location of their servers. The terms dark web and deep web are perceived to be linked with illegal and otherwise suspicious activity; however, a vast difference exists between the two.
So hey, we’ve beaten around the bush quite a bit, let’s finally get you what you came here for, here’s how to access the deep web. First of all, you need to make sure there are no digital traces leading back to you associating you with your deep/dark web activities. (The isn’t list I believe is non-existent when it comes to the Dark web). I just mentioned the Tor network, and it’s a major part of both the deep as well as the dark web so let me explain what it is in brief.

Bitsight’s 2025 deep web intelligence shows how cybercriminals are multiplying, diversifying—and getting smarter. The US government created the dark web to help its spies communicate and exchange information securely. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails.