Not only do cybercriminals use it, but Dread has also become a go-to source for cybersecurity professionals to spot emerging threats, track criminal groups, and even understand the trends in the dark web market. Discover the top thirteen dark web forums where cybercriminals gather and cybersecurity researchers spot emerging threats. It has built a reputation for being a reliable source of stolen credit card data and PII.
Sale Of Stolen Data

Law enforcement agencies actively monitor these markets and can track users despite anonymity measures. Financial fraud is common, and you have no recourse if transactions go wrong since these markets operate outside legal frameworks. Activities on dark-web marketplaces are closely monitored by international law enforcement agencies. Purchasing or selling illegal goods—such as controlled substances, counterfeit documents, or stolen data—can result in significant legal penalties, including fines, criminal charges, and imprisonment. Even users who access these platforms without intent to buy illegal items risk suspicion or investigation.
Top 5 Hacker Forums On The Deep And Dark Web In 2022

‘Do it yourself’ is fun most of the time, but we recommend not taking that approach in this case. Several dark web monitoring tools exist that today have automation capabilities that users and companies can rely on. In the current digital era, where cybercrimes are constantly rising, individuals and businesses need to up their protection techniques. One of the best ways to ensure proper online security is to implement dark web monitoring. Some of the reasons why it’s worth monitoring these hack forums include, ability to detect breaches early, gaining threat actor insights, and third-party risk mitigation. If you’re a company, you might want to monitor the dark web to safeguard your reputation and compliance.
Cryptostamps
I had talked to some of the godfathers of the Argentine hacking scene who really made clear that Argentina had become what they called the India of exploit development. That is, people outsource a lot of their software engineering to India and in their minds, Argentina had become this big outsourcing hub for exploit development. This is where governments and front companies and brokers came to purchase zero-day exploits that they could use for their stockpiles of offensive cyber-espionage tools. So, one night I went out, and I had always been really careful to bring basically pen and paper to these conferences. The concept of darknets emerged as a response to concerns about digital privacy and government surveillance.
Supporting BTC (65%) and XMR (35%), Alphabay’s interface features multi-language support and real-time analytics (4.9/5 vendor score across 100,000+ reviews). Its history—$600M trades pre-2017 bust, relaunched in 2021, and 25% listing growth in 2025—shows resilience. Alphabay’s top-tier status stems from its scale, reliability, and advanced features, though peak-hour lag slightly tempers its rank. ASAP’s payment system scores a 94% success rate, clearing 90% of disputes in 36 hours—solid for its size. Its Tor routing keeps a 93% uptime, with dips linked to adding new currency options, not outside hits.
Story Of The Year: Global IT Outages And Supply Chain Attacks
Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project). These technologies obscure users’ identities and locations by routing their internet traffic through multiple volunteer-operated servers worldwide, making it extremely difficult to trace activities back to individuals. Tor remains the most prevalent method due to its ease of use and robust anonymity features, but the popularity of I2P is steadily growing due to its increased resistance to surveillance and censorship.
Perhaps one of the major attraction factors of these forums is undoubtedly anonymity. Cybercriminals want to carry out their illegal activities without detection by law enforcement agencies and other authorities. CryptBB focuses on the exchange of advanced hacking tools, stolen identity logs, and various exploitation techniques.
China-based Vendors And Novel Synthetic Opioids
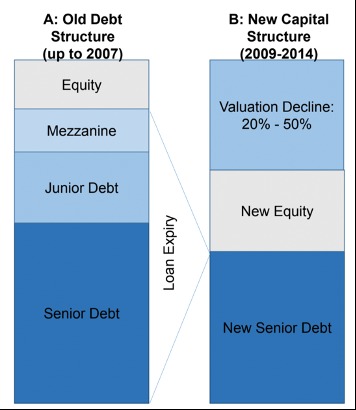
This often involves joint operations between national police forces, intelligence services, and specialized cyber units. By pooling resources and expertise, they can develop new techniques for unmasking hidden servers or tracing cryptocurrency flows. Bitcoin remains the most widely recognized, though it has become easier to trace through blockchain analytics. As a result, privacy-focused coins like Monero and Litecoin have gained traction among those seeking tighter anonymity. Some marketplaces also explore emerging alternatives, offering greater obfuscation techniques to bypass law enforcement surveillance.
Is It Illegal To Access The Dark Web?
Some use them due to privacy concerns, such as journalists talking to informants or whistleblowers, while others may simply want to protect their confidential information from observation or tracking. Nevertheless, most people on the internet do not need to communicate or venture into the dark web. By understanding its intricacies and the nature of threat actors like IABs, organizations can build robust defenses, effectively neutralizing these threats and securing their critical digital assets. In the face of an ever-evolving cyber threat landscape, punctuated by the proliferation of platforms like Exploit and the rise of IABs, fortifying cyber defenses has never been more crucial. There are several strategic steps that organizations can take to effectively respond to these threats originating from the dark web.
While law enforcement regularly shuts down illegal marketplaces, the underlying infrastructure remains functional. New darknet sites and markets continuously emerge to replace those that get shut down. The technology behind the darknet is actively maintained and continues to evolve. Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents.
Verify Onion Links Religiously
- I’ve been called out on this for saying some of them were Middle Eastern but I mean, some of them spoke Arabic.
- Some of the costs can be much higher if they come in a bundle and may also include how-to tutorials on making the most out of the credit cards to conduct fraud.
- If, for example, a breach exposed your financial information, you’ll need to check your bank statements for any suspicious transactions.
- Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools.
- Nevertheless, the digital landscape is under constant cyber threat, and individual or business data can find its way onto the dark web.
It’s a platform for both beginners and elite hackers where they share knowledge on a wide range of topics like carding and advanced hacking techniques. Moreover, the forum offers discussions around account credential dumps, financial crime tools, and various network infiltration strategies. Exploit.In is one of the most visited (and notorious) dark web platforms from long ago, which operates in a Russian-speaking landscape.
Criteria For Choosing The Best Dark-Web Marketplaces
However, the zero-day exploit market is atypical and the way it operates is closer to the workings of the black market. Brokers and bounty programs, which could be seen as retailers of zero-days, have no control whatsoever on the original producers of the “bad” as they are independently discovered by different, and often anonymous, actors. It is not in their interest to change the channel of distribution as they can profit from both the white and gray markets, having much less risk in the former. Gray markets buyers include clients from the private sector, governments and brokers who resell vulnerabilities. We need people who understand this even at a basic level so they can make good decisions for our future. For the last few decades, countries around the world have been watching the US to see how they should act when conducting digital espionage.